Authentication¶
See the topics given below to manage authentication for your applications.
Design the login flow¶
When you register an application, you can customize the login flow.
-
Configure WSO2 Identity Server login for single-page applications with OIDC or web applications with OIDC or SAML.
-
Add social login options such as Google, Facebook, Apple, and Microsoft.
-
Add other enterprise identity providers as login options.
-
Configure the number of factors (2FA or MFA) in the login flow to enforce multi-factor authentication.
-
Enforce conditional authentication to dynamically change the login flow of a user based on the user's devices, networks, locations, or usage contexts.
-
Add SSO integrations using WSO2 Identity Server to log in to applications such as Google, Salesforce, Microsoft, Zoom, and Slack.
Manage user attributes¶
Manage the user attributes you want to share with your application:
Manage connections¶
External Identity Providers (IdPs) can be registered as connections in WSO2 Identity Server and be used to authenticate users who log in to your applications. These IdPs authenticate users and issue identification information using security tokens based on protocols like SAML 2.0, OpenID Connect, OAuth 2.0, and WS-Trust. This process of authenticating users with external IdPs is known as Identity Federation.
With identity federation, users can use an existing user account registered to a trusted IdP to login to your applications without having to create accounts for them in WSO2 Identity Server.
Note
If the IdP is configured to use JIT user provisioning, when a user signs in with an external IdP, an account will automatically be created for the user in WSO2 Identity Server.
Supported external IdPs¶
WSO2 Identity Server supports a variety of external identity providers with various open-standard protocols (such as OAuth2.0, OpenID Connect, and SAML).
You can configure any number of external connections for your application via WSO2 Identity Server.
Map local attributes to external attributes¶
Follow the steps below to map attributes of WSO2 Identity Server with that of a connection.
-
On the WSO2 Identity Server Console, go to Connections.
-
Select your connection and go to its Attributes tab.
-
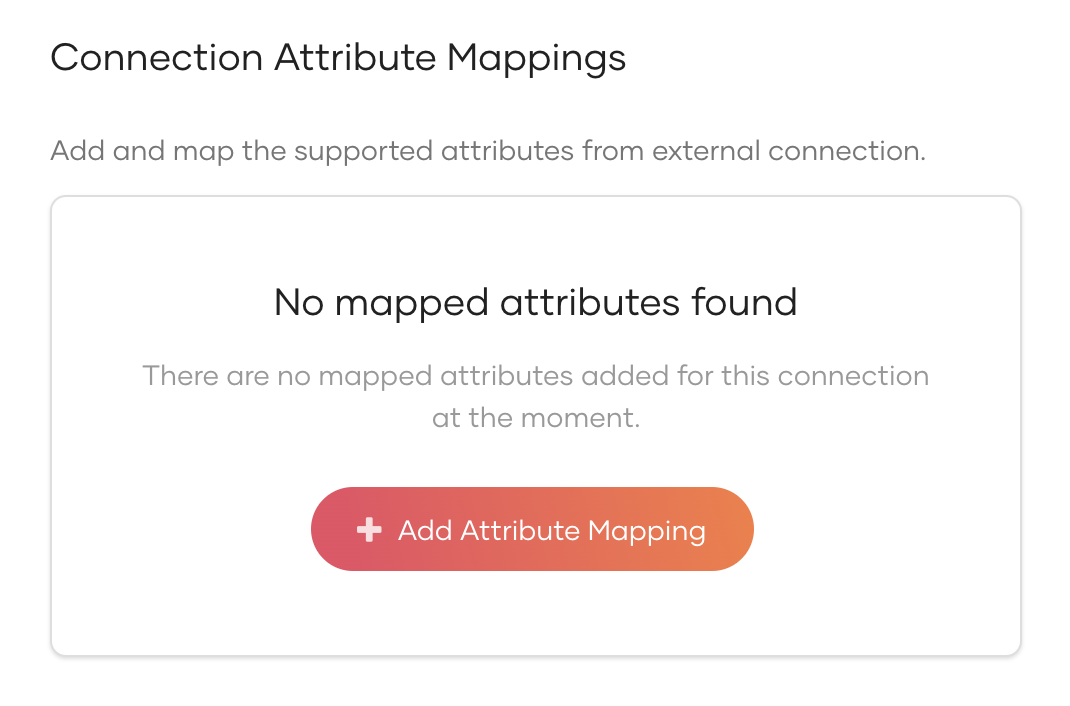
Click Add Attribute Mapping to add a new attribute mapping.
-
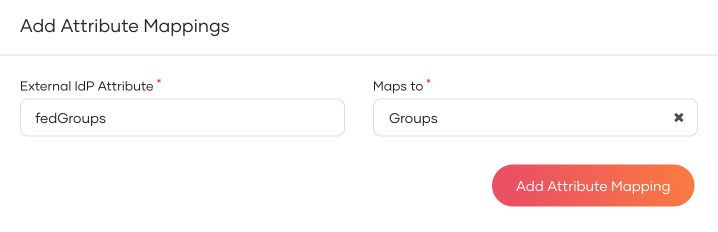
Enter the External IdP Attribute of the connection and map it to the Groups attribute of WSO2 Identity Server.
-
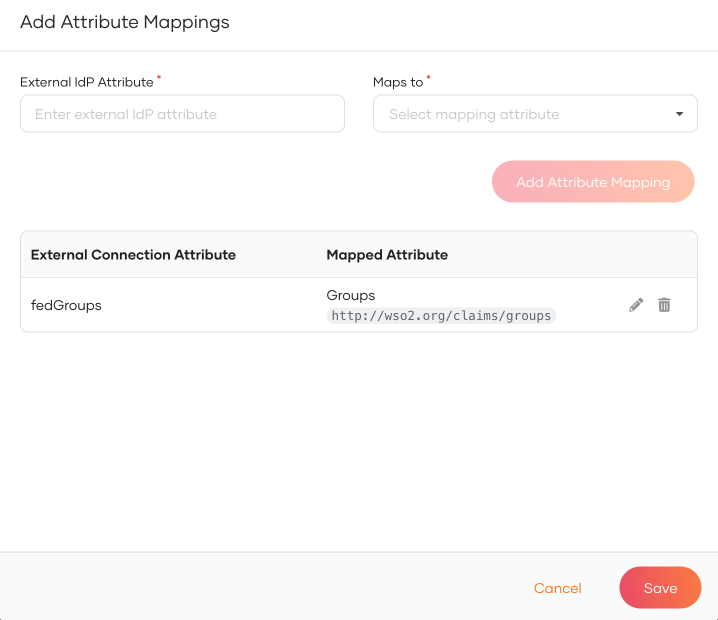
Click Add Attribute Mapping and then click Save.
-
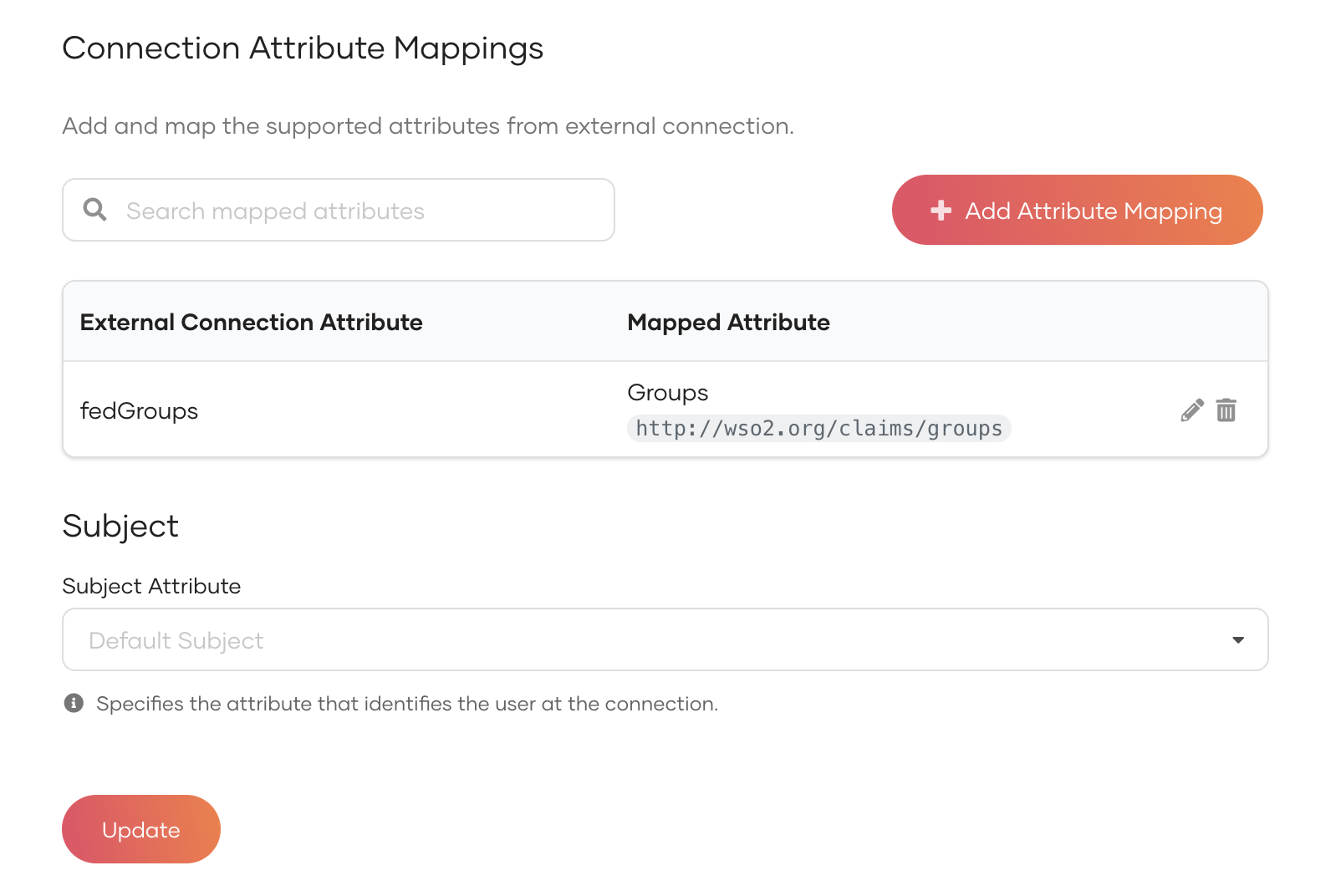
Click Update to save the changes.
Add required attributes for provisioning¶
When provisioning users from an external identity provider (IdP), you may want to include specific attributes in the user’s profile. Follow the steps below to define the required attributes and assign default values.
- On the WSO2 Identity Server Console, go to Connections.
- Select your connection and go to its Attributes tab.
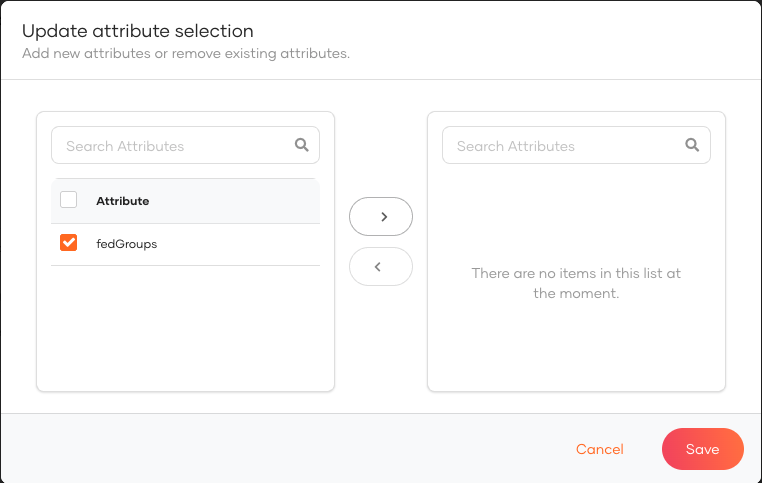
- Under Provisioning Attributes Selection, click Add Attribute.
-
Move the attributes that you want to include in the provisioned user's profile and click Save.
-
Add a default value to the attribute. If the federated user lacks data for it, the system adds the default to the provisioned user’s profile.
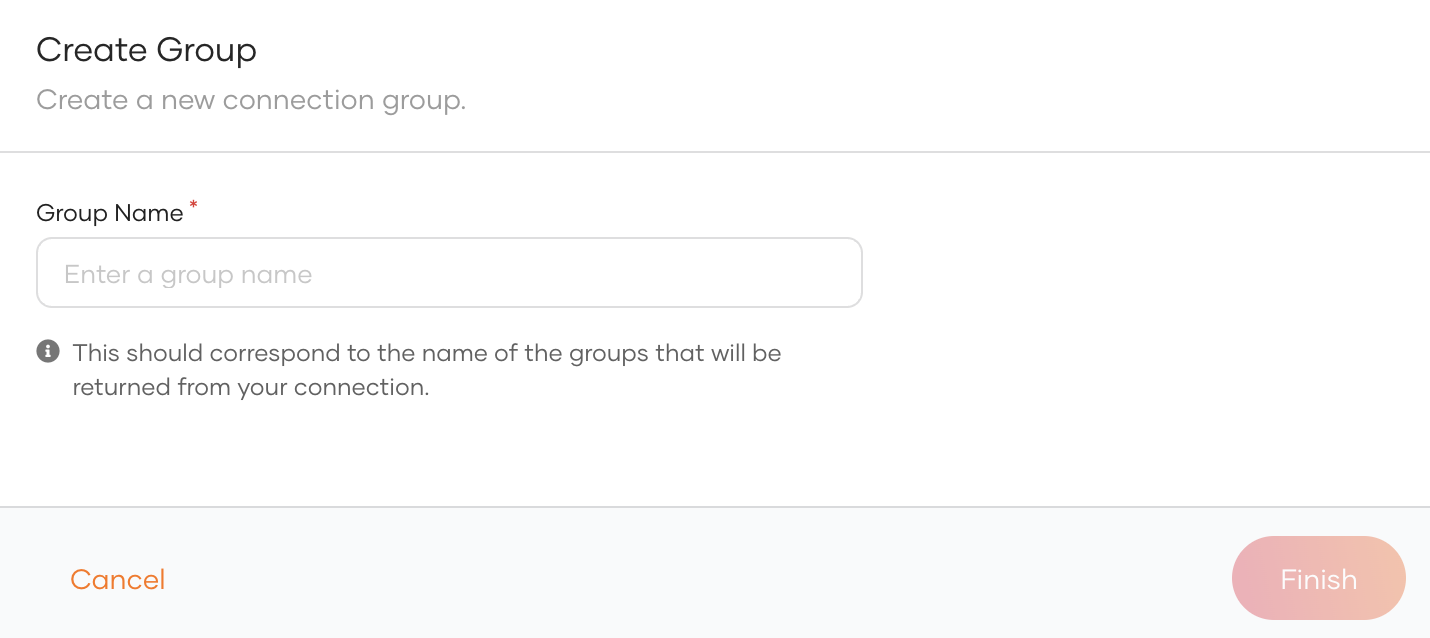
Add groups to connections¶
Follow the steps below to add the groups from your connection to WSO2 Identity Server: