Validating OAuth Access Token Scope Using XACML Policies During Token Issuance¶
To provide fine-grained access control to APIs, WSO2 Identity Server allows validating the scope of an OAuth access token using XACML policies during the token issuing phase.
If you want the XACML scope validator to execute when issuing an access token in an OAuth access token issuing flow, you can select the scope validator as XACML when you configure a service provider. This provides fine-grained access control to APIs.
Follow the steps below to configure WSO2 Identity Server to validate OAuth access tokens scopes using XACML policies.
Configuring the service provider¶
To configure the client application as a service provider in WSO2 Identity Server:
-
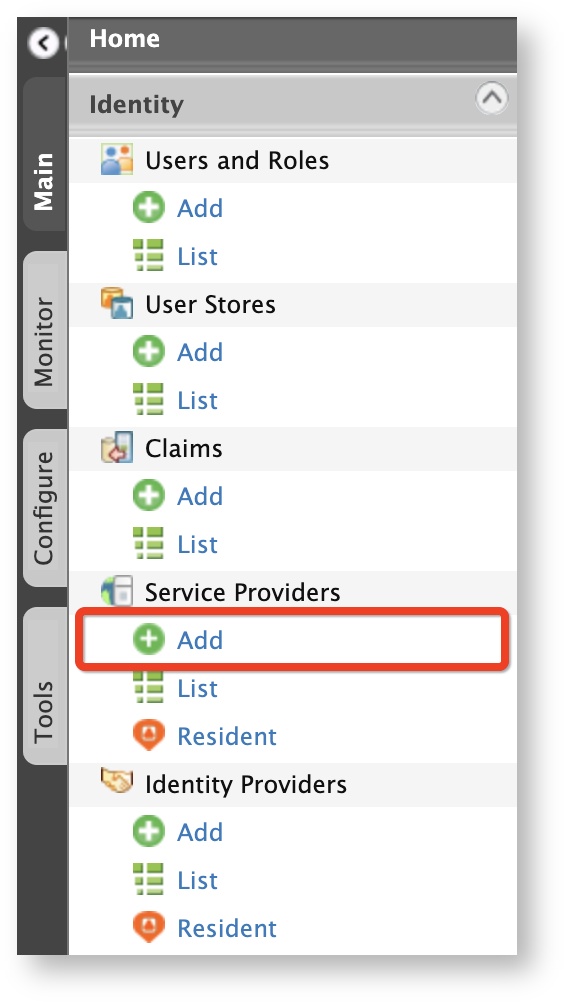
On the Main menu of the Management Console, click Identity > Service Provider > Add.
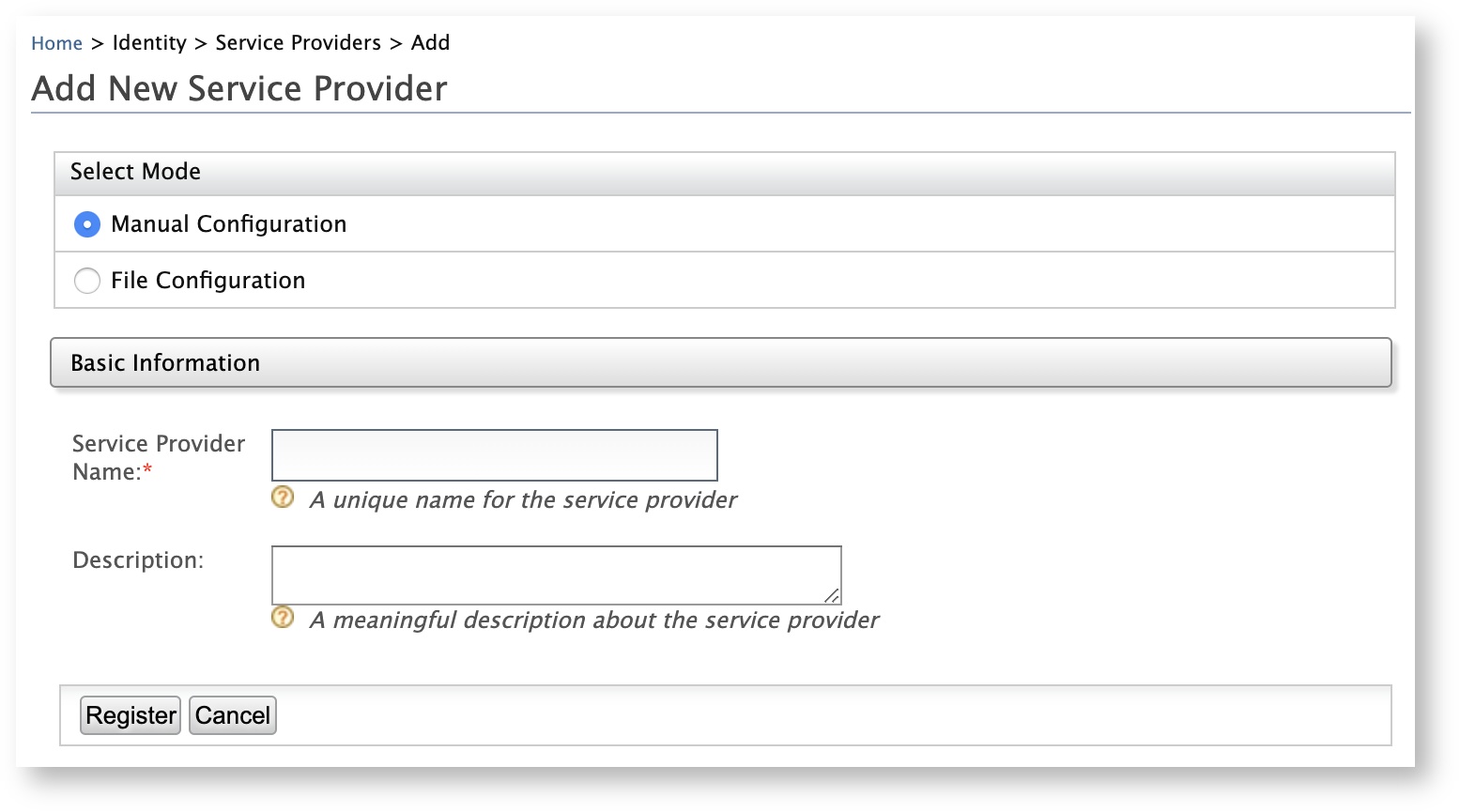
The Add New Service Provider screen appears.
-
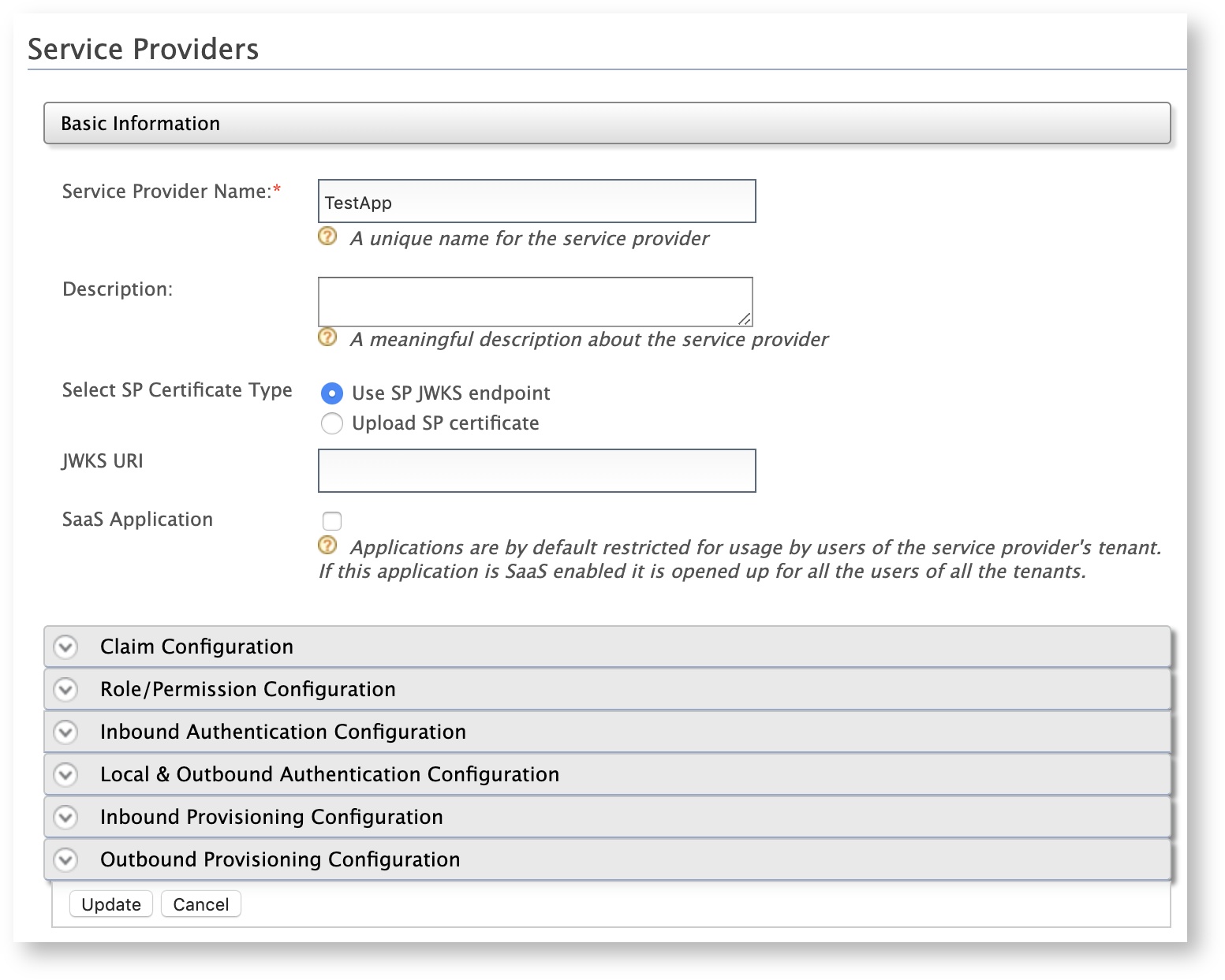
Enter a meaningful name for the client application in the Service Provider Name text box and click Register. The Service Providers screen appears.
-
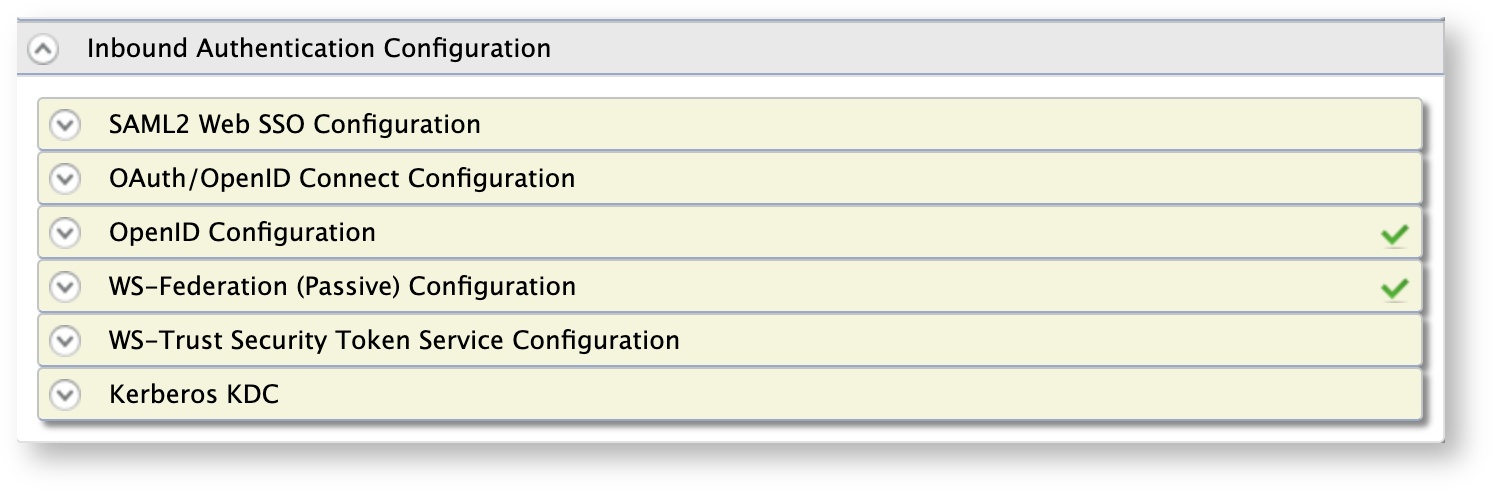
Under the Inbound Authentication Configuration section, click OAuth/OpenID Connect Configuration > Configure.
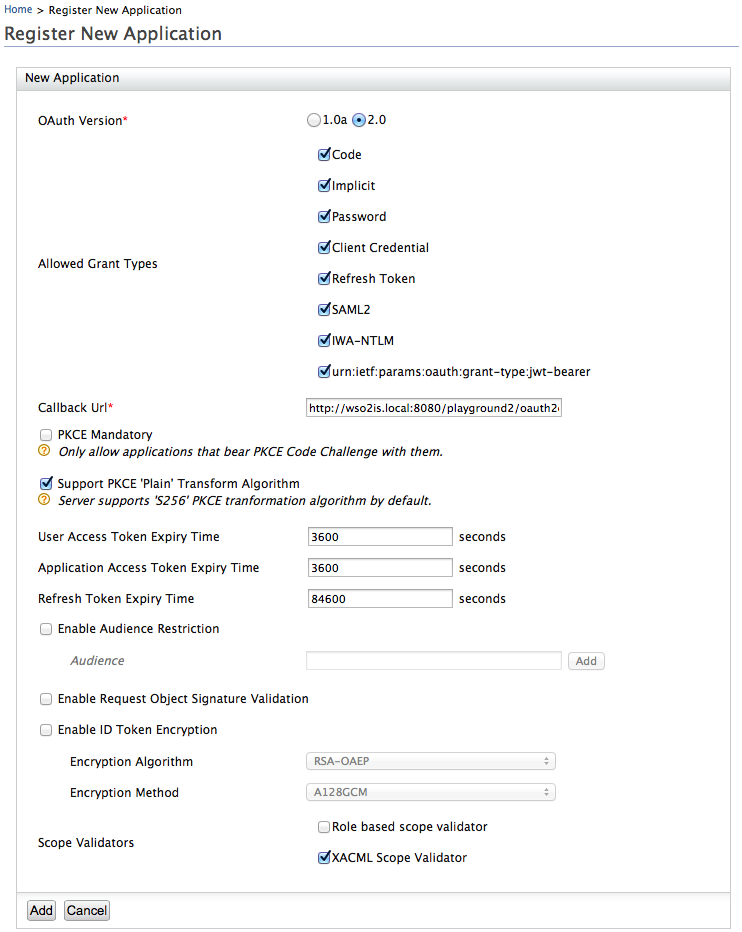
The Register New Application screen appears.
- Enter the
callback URLor your application in the Callback Url text box. - Select the XACML Scope Validator check box under Scope Validators.
- Click Add.
You have successfully added and configured the service provider. Next, we will learn how to configure a XACML policy to validate the OAuth access token scopes that are used to authenticate the access requests for the client application.
Setting up the XACML policy¶
To publish a XACML policy using a default XACML policy template in WSO2 Identity Server:
-
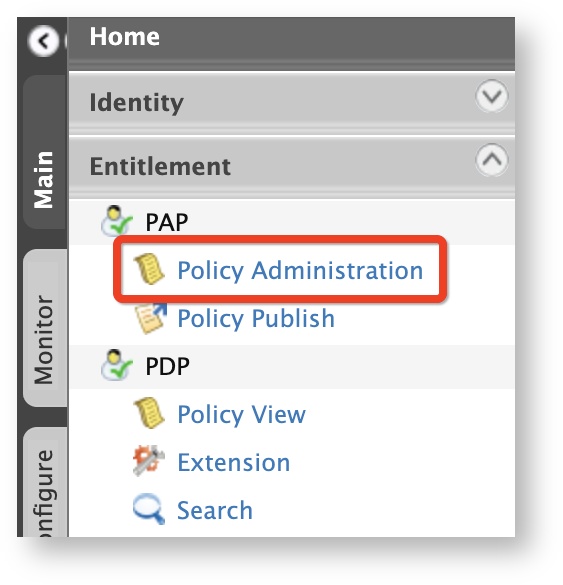
On the Main menu of the Management Console, click Entitlement > PAP > Policy Administration.
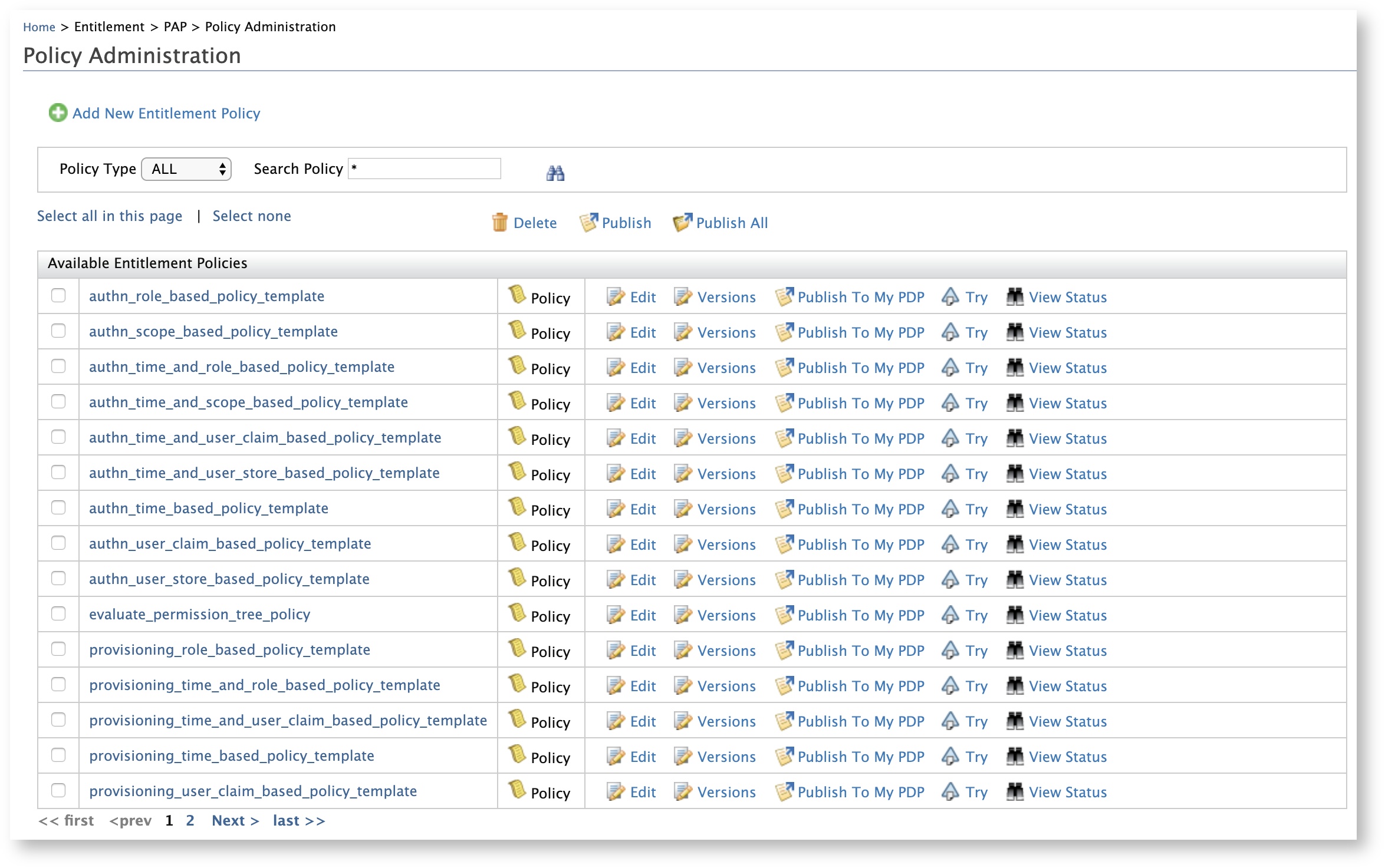
The Policy Administration screen appears.
-
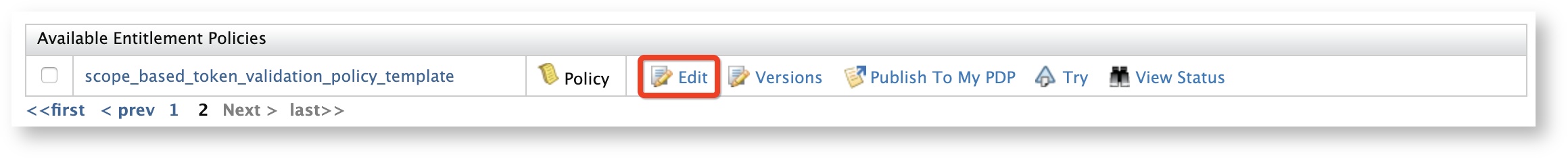
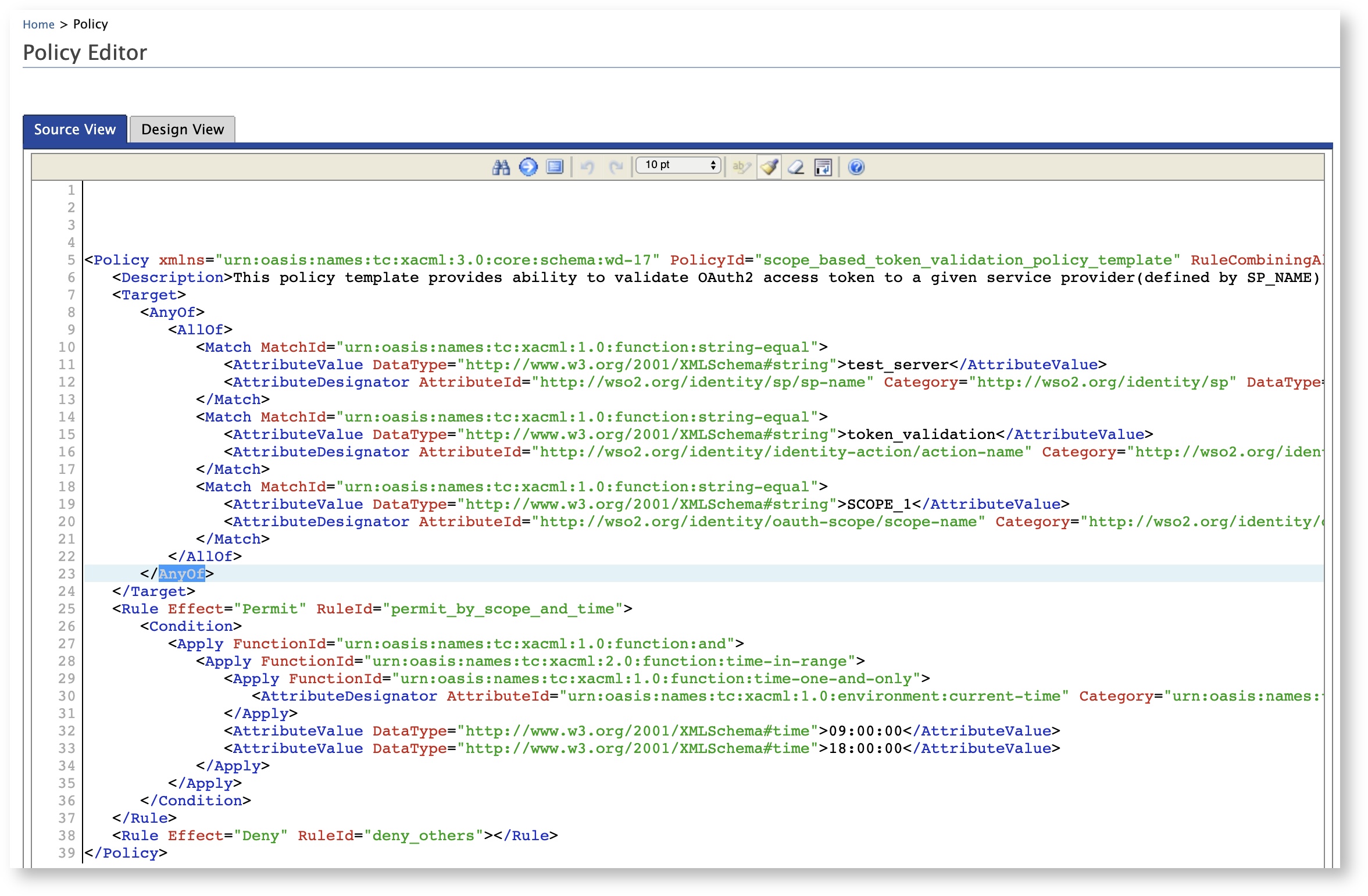
Click Edit of the scope_based_token_issuance_policy_template policy.
The Policy Editor appears with the pre-configured template with place holders.
-
Edit the policy as required including the PolicyId and click Save.
A new policy with the changes you made to the template appears with the policy ID you added. (The original policy is intact)
-
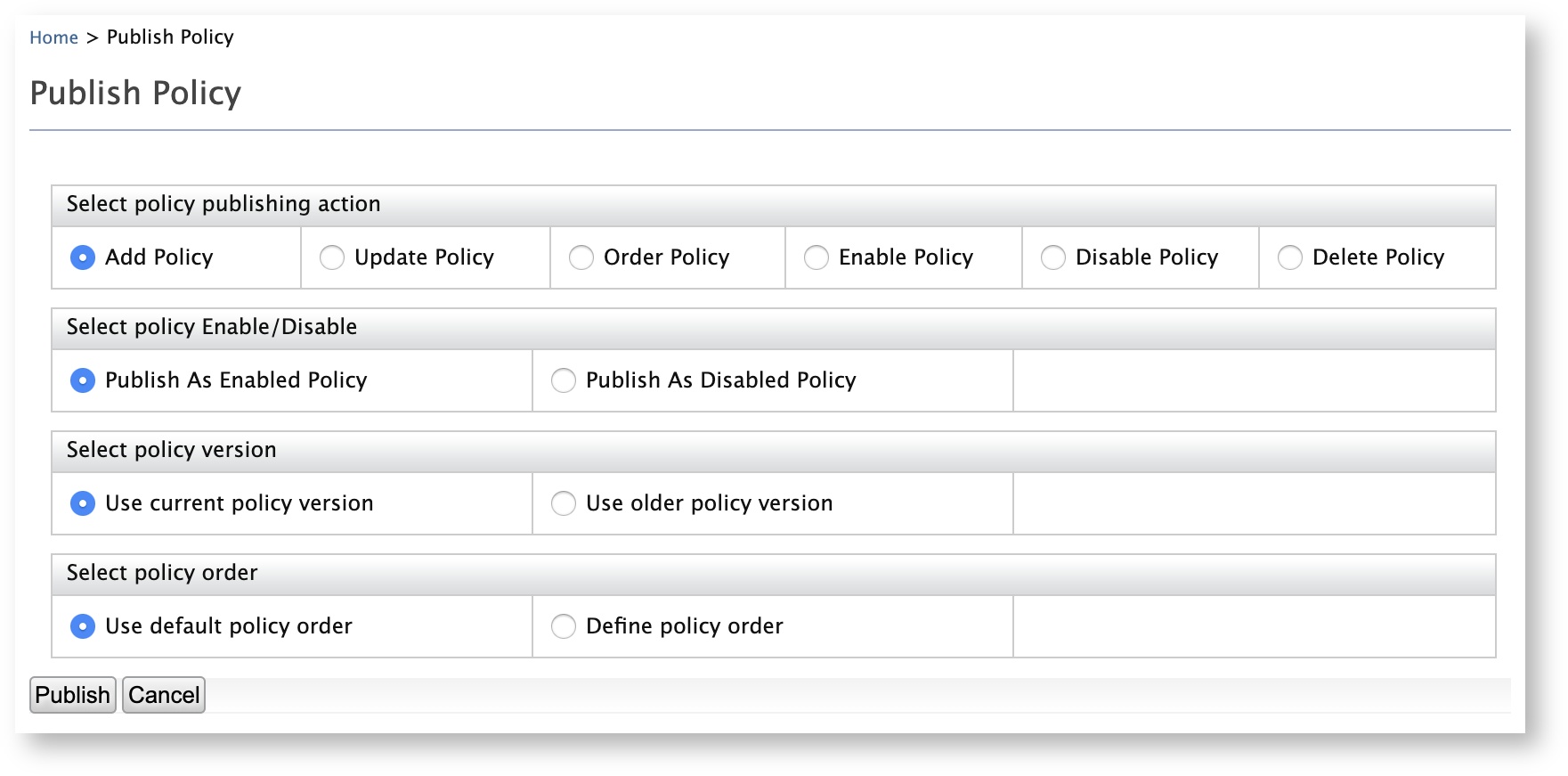
Click Publish To My PDP of the new policy. The Publish Policy screen appears.
-
Leave the default values as they are and click Publish.
Tip
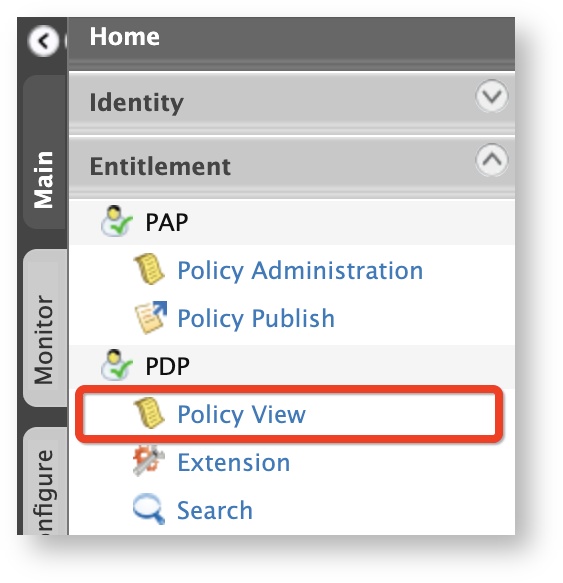
To ensure that the policy has been successfully published:
Info
- For more information on Policy Administration Point (PAP), see [Configuring the Policy Administration Point.
- For more information on publishing XACML policies, see Publishing a XACML Policy.
You have successfully published a XACML policy. Let's test the policy to evaluate whether the XACML scope is validated during OAuth token issuance.
Try it out¶
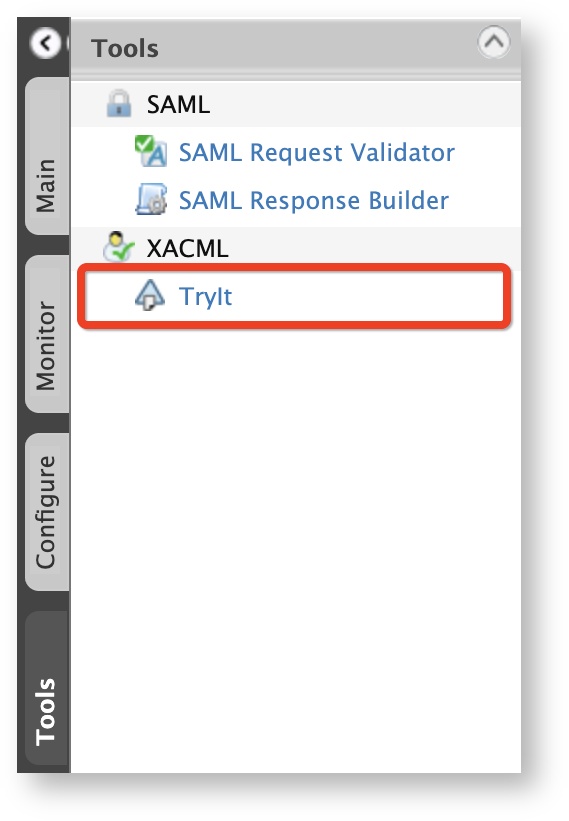
The XACML TryIt tool allows you to test the policies easily without having to create and send authorization requests to WSO2 Identity Server. It is a tool through which authorization requests can be created and evaluated against the available policies. You can write simple XACML 3.0 requests in XML format and try them using the web UI of the TryIt tool.
To try out the policy using the XACML TryIt tool:
-
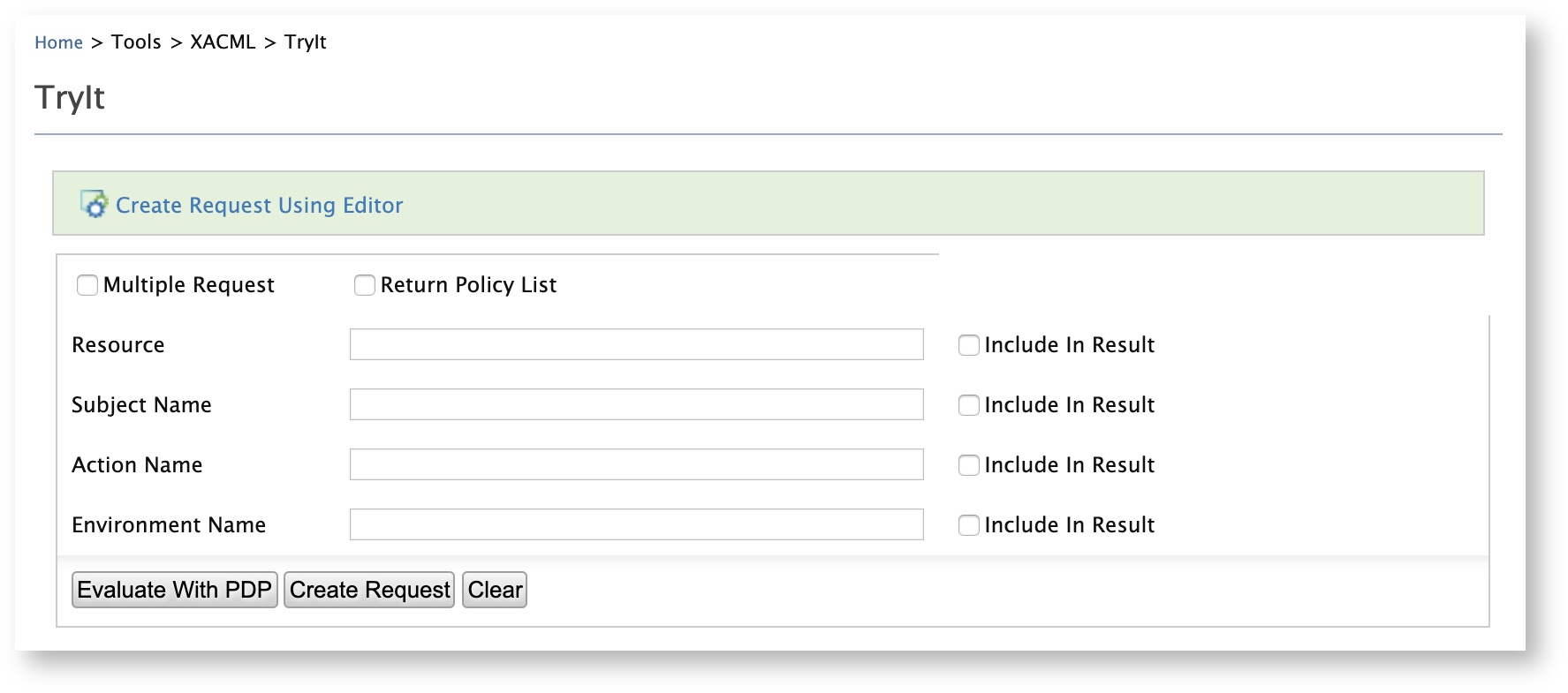
On the Tools menu of the Management Console, click XACML > TryIt.
-
The TryIt screen appears.
-
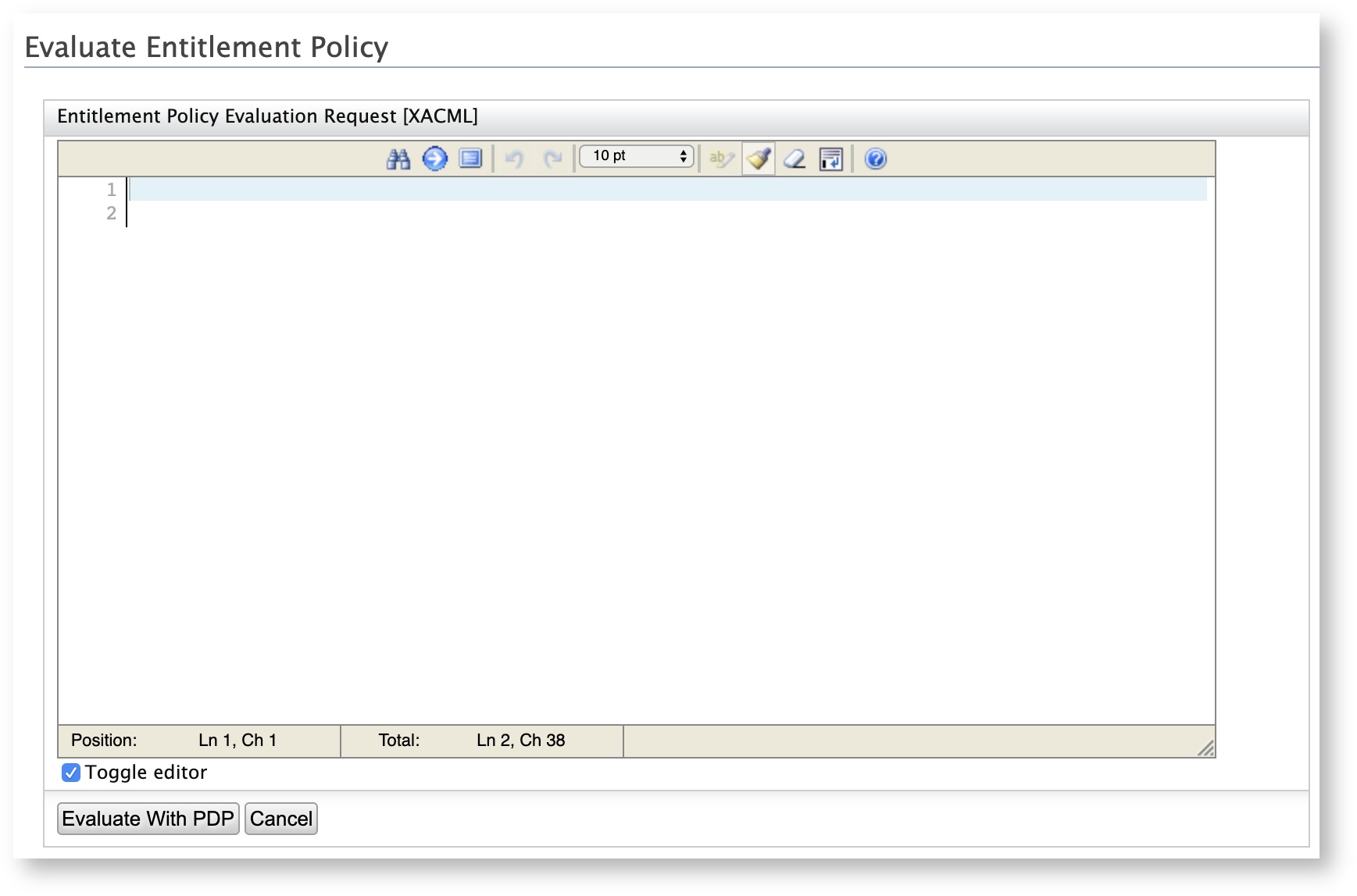
Click Create Request Using Editor. The Evaluate Entitlement Policy screen appears.
-
Enter the following as the sample request and click Evaluate With PDP.
playground2 scope_validation SCOPE_1 A response message with either Permit or Deny appears based on the XACML scope validation during token issuance.
Note
For backward compatibility, you can disable this validation by setting the following property value to true in the
deployment.tomlfile in the[IS_HOME]/repository/confdirectory.[oauth.scope_validator.authz_implicit] enable = false
Top