Changing the Authentication Endpoint¶
The authentication endpoint is the authentication URL used in authentication requests. The following sections discuss methods of customizing this endpoint for various scenarios.
Customizing the authentication endpoint URL¶
The authentication endpoint URL is the location in your web application that contains authentication related pages.
Follow the steps below to customize the authentication endpoint URL:
-
Add the following configurations to the
<IS_HOME>/repository/conf/deployment.tomlfile, and change the value of the login_url parameter depending on the URL on which the web application should run.[authentication.endpoints] login_url="/sso/login"Note
If you do not change the default value of this configuration, accessing the dashboard redirects you to the WSO2 Identity Server management console.
-
Run the web application on the new authentication endpoint URL.
Controlling the request parameters going to the authentication endpoint¶
Additional request parameters can be added and customized for the
request sent to the authentication endpoint. To customize this,
add the following configurations in the
<IS_HOME>/repository/conf/deployment.toml
file.
[authentication.endpoint.query_params]
filter_policy = exclude
filter_parameters = [username]
filter_parameters = [password]Note
In the above configuration, username and password are just given as examples. You can configure any query parameter here for your request and customize it according to your specifications.
Loading tenants into the dropdown in the login page of the authentication endpoint web application¶
This section is useful in scenarios where there are multiple tenants used, where users can login to web applications with their credentials for their specified tenants. For instance, for a user in the test.com tenant with the username test1, the user would have to enter the full username as "[email protected]" in order to login. Enabling this feature will load all the available active tenants onto a dropdown list on the login page of the web application that the authentication endpoint points to. This means that the test1 user mentioned above can simply select the tenant he/she belongs to (test.com) from the dropdown list and only needs to enter the username (i.e., test1) in the username textbox on the login page, without having to type it with "@tenant-domain".
Do the following configurations to enable this feature.
-
Add the following configuration to the
<IS_HOME>/repository/conf/tomcat/deployment.tomlfile and ensure that theclientAuthattribute in theConnectortag is set to “ want ” as shown below. This is done to disable the certificate authentication on certain occasions (like when working on mobile apps). This makes two-way SSL authentication optional.[transport.https.properties] clientAuth="want"Info
The
.jarfile enabling usage of Mutual SSL is shipped with IS by default from IS versions 5.1.0 and upwards. Theorg.wso2.carbon.identity.authenticator.mutualssl_X.X.X.jarfile can be found in the<IS_HOME>/repository/components/pluginsdirectory. -
Open the
<IS_HOME>/repository/conf/deployment.tomlfile and add the following parameter to enable the Mutual SSL Authenticator.[admin_console.authenticator.mutual_ssl_authenticator] enable = true -
If the
saml_sso_authenticatoris enabled in the<IS_HOME>/repository/conf/deployment.tomlfile, set its priority to 0. Otherwise ignore this step.[admin_console.authenticator.saml_sso_authenticator] enable = true priority = 0 -
Add the following configuration into the
/repository/conf/deployment.toml`. [tenant] data_listener_urls = ["url1","url2"] [tenant.domain_drop_down] enable = trueNote
When configuring the
TenantDataListenerURLtag, note the following.-
In a clustered setup that has multiple authentication endpoint web applications hosted, list all of them under the
TenantDataListenerURLtag. -
For authentication endpoint web applications hosted outside the WSO2 Identity Server or in other nodes of a cluster, add the absolute URL within the
TenantDataListenerURLtag.
-
-
Restart the server using one of the following commands.
-
Windows :
wso2server.bat -
Linux/Unix :
sh wso2server.sh
-
-
Once the server is restarted, the authenticationendpoint.war file is deployed. The
<IS_HOME>/repository/conf/deployment.tomlfile has to be configured with the required values for properties. The following are the default values for the properties to be used in this file.[identity.auth_framework.endpoint] tenant_list_enabled="false" hostname_verification_enabled="true" mutual_ssl_username="admin" client_keystore="wso2carbon.jks" carbon_security_keystore_password="wso2carbon" client_truststore="client-truststore.jks" carbon_security_truststore_password="wso2carbon" identity_server_service_url="https://localhost:9443/services/" username_header="UserName"Do the following updates to this configuration.
- Set
tenant_list_enabledtotruein order to enable the tenants to display as a list. -
For the
mutual_ssl_usernameproperty, set the username that is to be used for mutual SSL authentication. This user needs to have permission to list down tenants. You can add a new username here provided that you create a user with that username and grant the following permissions to the role of the user.Super Admin Permissions > Manage > Monitor > Tenants > List
-
Paths for client keystore and truststore can be relative paths or absolute paths. The default paths point to the keystore and truststore of the Identity Server itself. A new keystore can be created and used for the client if necessary, however, you must set the passwords for
carbon_security_keystore_passwordandcarbon_security_truststore_passwordappropriately.
Note
If you are hosting the
autheticationendpoint.warwebapp outside the Identity Server (i.e in a different Tomcat or WSO2 Application Server), then you cannot use the<IS_HOME>/repository/conf/deployment.tomlfile because the webapp does not have access to this file. Instead, the same property file can be found at<WebApp_HOME>/authenticationendpoint/WEB-INF/classes/EndpointConfig.properties.In this scenario, do the following:
-
Open the
<WebApp_HOME>/authenticationendpoint/WEB-INF/classes/EndpointConfig.propertiesfile and provide the full URL to WSO2 Identity Server’s admin services endpoint in theidentity.server.serviceURLproperty following the format below.identity.server.serviceURL=https://: /services -
Copy the
org.wso2.carbon.identity.application.authentication.endpoint.util-5.0.7.jarfile and paste it in the<WebApp_HOME>/authenticationendpoint/WEB-INF/libfolder.- If you have applied the
WSO2-CARBON-PATCH-4.4.0-0073security patch, copy the.jarfile found in the/patch0073 - If you have not applied the
WSO2-CARBON-PATCH, copy the.jarfile found in the/repository/components/plugins
- If you have applied the
- Set
-
For mutual SSL authentication, the public certificate of the Identity Server has to be imported to the truststore of the client and the public certificate of the client has to be imported to the client-truststore of Identity Server.
Sample commands
The following two commands are examples if you are using the keystore and client-truststore of the Identity Server itself for the client. This is executed from the
<IS_HOME>/repository/resources/securitydirectory.keytool -export -alias wso2carbon -file carbon_public2.crt -keystore wso2carbon.jks -storepass wso2carbonkeytool -import -trustcacerts -alias carbon -file carbon_public2.crt -keystore client-truststore.jks -storepass wso2carbonNote
If you are not using mutual SSL authentication, you can stop the MutualSSLManager from loading the keystore by setting the
mutual_ssl_manager_enabledproperty in thedeployment.tomlfile to false. This property is enabled by default.mutual_ssl_manager_enabled="false"
Removing the tenant list from the login page¶
If it is required to remove the tenant domain dropdown list in SSO Login page, follow the steps below.
- Shutdown the server if it is already started.
-
Set the
tenant_list_enabledproperty to false. -
Set following parameter to
false.[tenant.domain_drop_down] enable = true -
If the
MutualSSLAuthenticatoris only used for the purpose of listing tenant domains in the drop down, disable it in the<IS_HOME>/repository/conf/deployment.tomlfile.[admin_console.authenticator.mutual_ssl_authenticator] enable = true -
Restart the server.
Handling browser back button and bookmarked login page¶
This section describes how to enhance the usability of authentication endpoint webapp with different user behavioral patterns. One such behavioral pattern is that the user may click the back button from authenticated application or keep the endpoint login page URL bookmarked. In such situations, the user should be directed to the appropriate page.
Let's see how this can be achieved.
First, you need to add a registry resource that will contain the redirect URLs of different service providers. To do that, follow the below steps:
-
Start the Identity Server and l og in to the Admin Console.
-
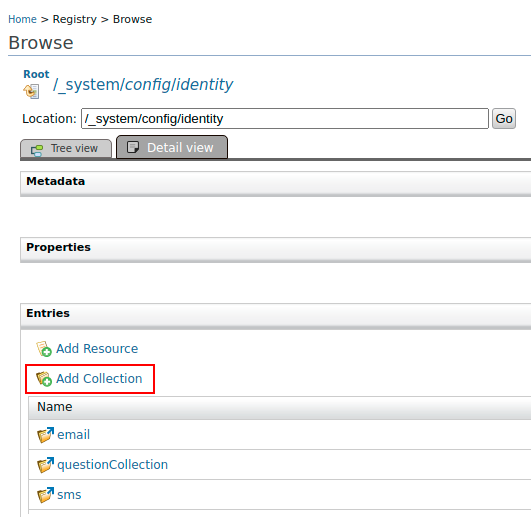
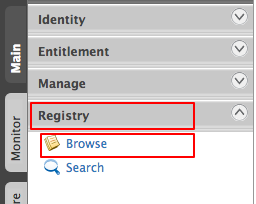
Click on Main Menu, under Registry, click Browse to see the registry browser.
-
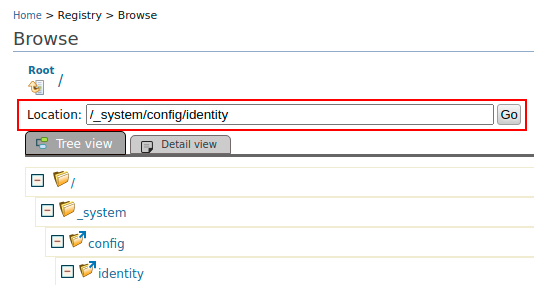
Browse the registry and go to
/_system/config/identity.
Once you navigate to/_system/config/identity, follow the steps below to add a registry collection. -
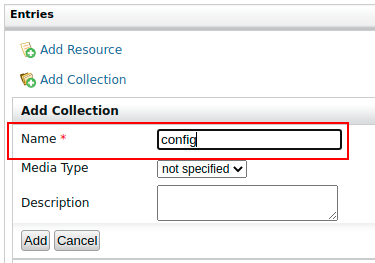
Fill the form with following information.
- Name : config
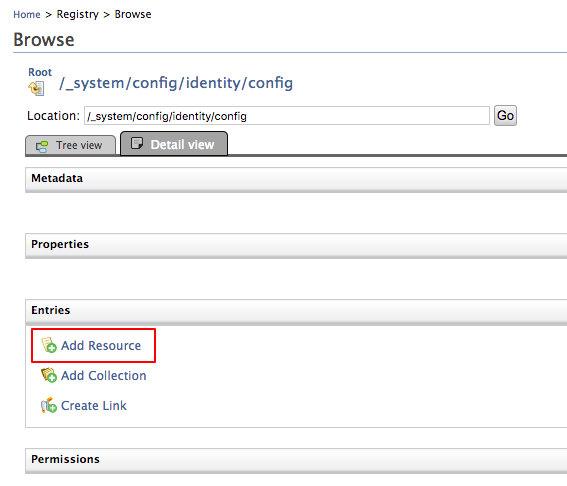
Once the Add button is clicked, it will navigate to the new collection
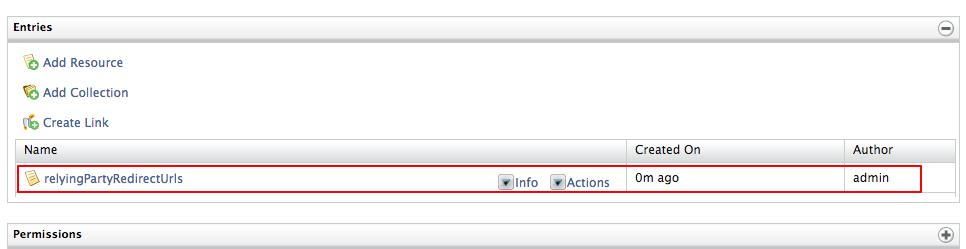
/_system/config/identity/config. Then, follow the steps below to add a registry resource. -
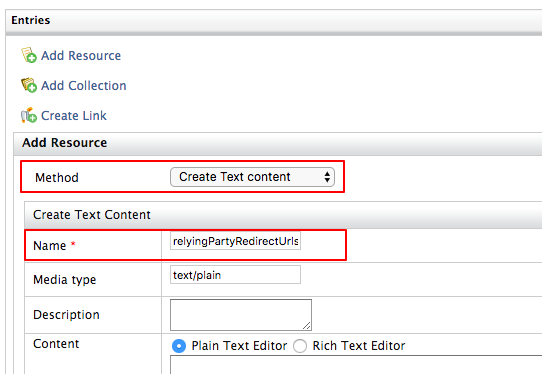
Fill the form with following information.
-
Method : Select Create text content from the dropdown.
-
Name : Enter relyingPartyRedirectUrls as Name.
-
-
Click the Add button. The created registry resource can be seen once you click on Add button.
-
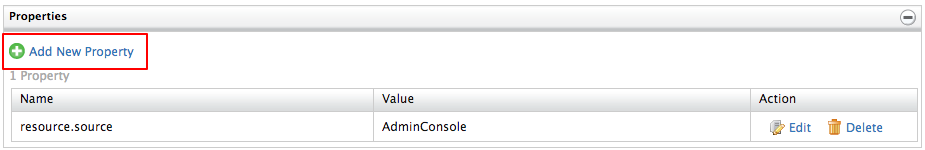
Click on the added resource (relyingPartyRedirectUrls). You can see the Properties section.
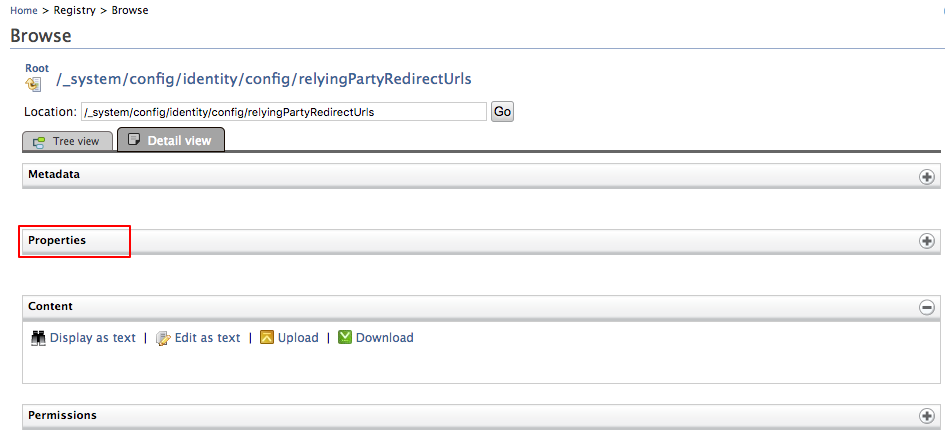
-
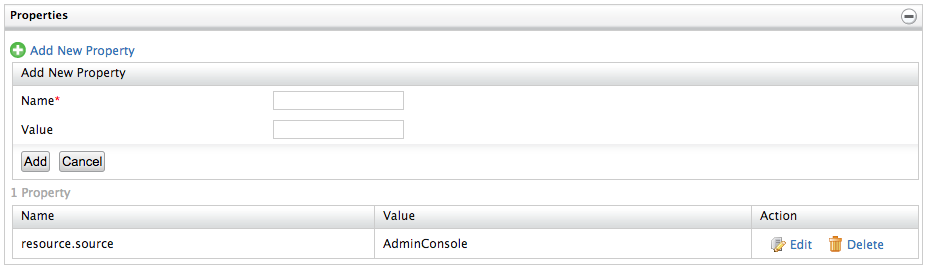
Click the “+” sign at the right hand corner of Properties section. This allows you to add a property to the resource.
-
Enter the relying party name for name and the redirect URL for value.
Info
-
Relying party name can be derived as below:
- Relying party name for SAML : Issuer Name
- Relying party name for OAuth2 : OAuth Client Key
-
Redirect URL is the URL you want the application to be redirected when the back button is pressed.
-
Relying party name with redirect URL needs to be configured like below:
<OAuth2_client_id>=<login_redirect_url><SAML_Issuer_Name>=<login_redirect_url>
-
Following are two sample values for Name and Value:
- Name : USER_PORTAL
- Value : https://localhost:9443/user-portal/overview
-
If you are using travelocity as the sample app, you can use the below values:
- Name : travelocity.com
- Value : http://localhost:8080/travelocity.com/home.jsp
-
-
Once you fill name and the value, click the Add button.
-
Now try out the back button and book marking scenarios.
Note
These configurations are per-tenant. You need to do this configuration after logging into Service Providers tenant Admin Console.