Forced Password Reset¶
The WSO2 Identity Server allows authorized administrative persons to trigger a password reset for a given user account. This may be required for the following situations:
- The user forgets the credentials and makes a request to the administrator for a password reset
- Credentials may get exposed to outsiders hence, the user needs to reset the password and lock the account, till then that no one else can log in.
In such situations, the user has the option of contacting the admin and based on the validity of the request, the admin can force a password reset for the user account. Once it is initiated, at the point of login, the basic authenticator processes the login request and prompts the corresponding dialogs or error messages based on account status.
The below steps describe how you can configure WSO2 Identity Server for forced password reset:
-
Enable the email sending configurations of the WSO2 Identity Server as explained here.
Tip
The email template used to send this email notification is the AdminForcedPasswordReset template for password recovery via recovery email, and the AdminForcedPasswordResetWithOTP template for password recovery via OTP (one-time password).
You can edit and customize the email template. For more information on how to do this, see Customizing Automated Emails.
-
If you wish to enable this feature for all tenants by default, add the following configureation to the
<IS_HOME>/repository/conf/deployment.tomlfile.[identity_mgt.password_reset_by_admin] enable_emailed_link_based_reset= true -
Start the Identity Server and log in to the management console with admin credentials.
-
Create a new user with the username "Alex" and update the user profile with a valid email address and other information.
-
Create a new role called "test role" with login permissions and assign it to the new user, "alex".
Tip
You can verify this by logging in to the user portal as Alex. The log in
attempt should be successful. Log out from the portal.
-
Click on Resident under Identity Providers found in the Main tab.
-
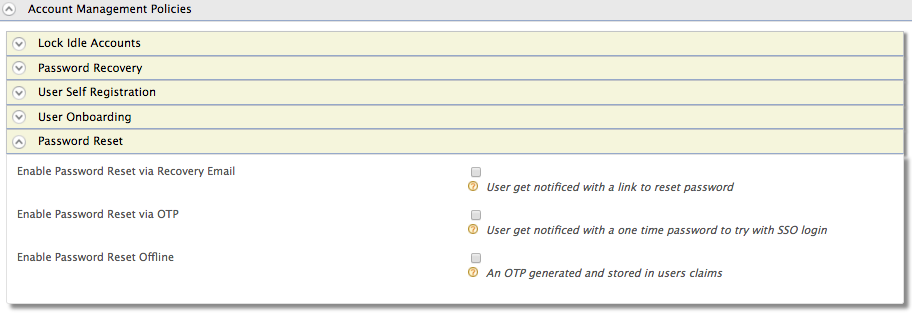
Expand the Account Management Policies tab.
-
Expand the Password Reset tab. You will see the following options for forced password reset:
Password Reset via Recovery Email¶
Enabling this option will send an email to the user with the
corresponding information. The email template for this option can be
configured in the email-admin-config.xml file found in the
[IS_HOME]/repository/conf/email/ directory under the
AdminForcedPasswordReset tag. Follow the steps below
to see a sample of how this works.
- Configure the properties mentioned above, start the Identity Server and navigate to the relevant interface.
- Select Enable Password Reset via Recovery Email from the three options listed, and click Update.
-
Once the option is selected, admin users can force a password reset flow by updating the
http://wso2.org/claims/identity/adminForcedPasswordResetclaim to 'true' for the relevant users. To do this, follow the steps explained later in this page under Invoke Admin Force Password Reset. -
Log out of the user portal and attempt to log in as the user you created above, "alex". The login attempt will fail and a password reset will be prompted in the form of an error message saying "Login failed! Please recheck the username and password and try again".
- Log in to the email account you provided in Alex's user profile. You will see a new email with a password reset request.
- Follow the link provided in the email to reset the password. You can now log in to the user portal successfully as Alex using the new password.
Password Reset via OTP¶
Enabling this option will send an email to the user with a one time
password that the user can use to log in once to the account after
which, the user will be prompted to set a new password. The email
template for this option can be configured in the
email-admin-config. xml file found in the
[IS_HOME]/repository/conf/email/ directory under the
AdminForcedPasswordResetWithOTP tag.
-
Configure the properties mentioned above, start the IS server and navigate to the relevant interface.
-
Select Enable Password Reset via OTP from the three options listed, and click Update.
-
Once the option is selected, admin users can force a password reset flow by updating the
http://wso2.org/claims/identity/adminForcedPasswordResetclaim to true for the relevant users. To do this, follow the steps explained later in this page under Invoke Admin Force Password Reset. - Log out of the user portal and attempt to login again as the user you created above, "alex". The login attempt will fail and a password reset will be prompted in the form of an error message saying "Login failed! Please recheck the username and password and try again".
- Log in to the email account you provided in Alex's user profile. You will see a new email with an OTP (one time password) provided to log in to the account.
- Use the OTP provided in the email to log in as Alex. You will be redirected to the password reset UI where you are prompted to set a new password. Enter the relevant details to set a new password.
- You can now log in to the user portal successfully as Alex using the new password.
Offline Password Reset¶
- Configure the properties mentioned above, start the identity server and navigate to the relevant interface.
- Select Enable Password Reset Offline from the three options listed, and click Update.
- Click on List under Claims found in the Main tab and select http://wso2.org/claims.
- Select the One Time Password claim, click Edit and select the Supported by Default checkbox. Click Update to save changes.
- Navigate to Users and Roles>List>Users and check the user profile of the user you created above (Alex). You will see that the value for the One Time Password field is empty.
- Next, admin users can force a password reset flow by updating the
http://wso2.org/claims/identity/adminForcedPasswordResetclaim to true for the relevant users. To do this, follow the steps explained later in this page under Invoke Admin Force Password Reset. - Log out of the user portal and attempt to log in again as the user you created above, "alex". The log in attempt will fail.
- Log in again to the management console as the admin user and check Alex's user profile. You will see that there is now a code value in the One Time Password field.
- Copy the code and use it as Alex's password to log in to the user portal.
- You will be redirected to the password reset UI where you are prompted to set a new password. Enter the relevant details to set a new password.
- You can now log in to the user portal successfully as Alex using the new password.
Invoke Admin Force Password Reset¶
Using SCIM 2.0 API¶
- Open the
scim2-schema-extension.configfile located in the<IS_HOME>/repository/conf/folder. -
Define the extension by adding the attributes in the following format before the last element of the JSON array in the
scim2-schema-extension.configfile.{ "attributeURI":"urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:forcePasswordReset", "attributeName":"forcePasswordReset", "dataType":"boolean", "multiValued":"false", "description":"Enable password change required notification in the user creation.", "required":"false", "caseExact":"false", "mutability":"readwrite", "returned":"default", "uniqueness":"none", "subAttributes":"null", "canonicalValues":[], "referenceTypes":[] }, -
Add the attribute names to the
scim2-schema-extension.configfile assubAttributesof the wso2Extension attribute as shown below.{ "attributeURI":"urn:ietf:params:scim:schemas:extension:enterprise:2.0:User", "attributeName":"urn:ietf:params:scim:schemas:extension:enterprise:2.0:User", "dataType":"complex", "multiValued":"false", "description":"Enterprise User", "required":"false", "caseExact":"false", "mutability":"readWrite", "returned":"default", "uniqueness":"none", "subAttributes":"verifyEmail askPassword employeeNumber costCenter organization division department manager forcePasswordReset", "canonicalValues":[], "referenceTypes":["external"] } -
Restart the server.
- Log in to the Management Console.
- Add a new external claim by following Main > Claims > Add > Add External Claim.
-
Add this new external claim under the
urn:ietf:params:scim:schemas:extension:enterprise:2.0:Userdialect as shown below. Make sure the name entered in the Dialect URI is the same as the one configured as theattributeURIin step 2.Field Value Dialect URI* urn:ietf:params:scim:schemas:extension:enterprise:2.0:User External Claim URI* urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:forcePasswordReset Mapped Local Claim* http://wso2.org/claims/identity/adminForcedPasswordReset -
Use the following SCIM 2.0 request to trigger a password reset.
You need to set the forcePasswordReset attribute under the
urn:ietf:params:scim:schemas:extension:enterprise:2.0:Userschema as true in the SCIM2 user create request.PATCH https://<host>:<port>/scim2/Users/<users-scim-id> {"schemas": ["urn:ietf:params:scim:api:messages:2.0:PatchOp","urn:ietf:params:scim:schemas:extension:enterprise:2.0:User"], "Operations": [ {"op": "add", "value": {"urn:ietf:params:scim:schemas:extension:enterprise:2.0:User": {"forcePasswordReset": true} }}] }A sample curl commands is given below:
curl -v -k --user admin:admin -X PATCH -d '{"schemas":["urn:ietf:params:scim:api:messages:2.0:PatchOp","urn:ietf:params:scim:schemas:extension:enterprise:2.0:User"], "Operations": [ {"op": "add","value": {"urn:ietf:params:scim:schemas:extension:enterprise:2.0:User": {"forcePasswordReset": true}}}]}' --header "Content-Type:application/json" https://localhost:9443/scim2/Users/c02857fd-2a51-427f-bf25-a9f76b85659d
Using SOAP Based admin services¶
- Discover the UserProfileMgtService admin service. For information on how to do this, see Calling Admin Services.
-
Create a new SOAP-UI project by importing above the WSDL: https://localhost:9443/services/UserProfileMgtService?wsdl.
-
Use the
setUserProfilemethod to send a SOAP request to update thehttp://wso2.org/claims/identity/adminForcedPasswordResetclaim of the project.Sample SOAP Request
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:mgt="http://mgt.profile.user.identity.carbon.wso2.org" xmlns:xsd="http://mgt.profile.user.identity.carbon.wso2.org/xsd"> <soapenv:Header/> <soapenv:Body> <mgt:setUserProfile> <mgt:username>tom</mgt:username> <mgt:profile> <xsd:fieldValues> <xsd:claimUri>http://wso2.org/claims/identity/adminForcedPasswordReset</xsd:claimUri> <xsd:fieldValue>true</xsd:fieldValue> </xsd:fieldValues> <xsd:profileName>default</xsd:profileName> </mgt:profile> </mgt:setUserProfile> </soapenv:Body> </soapenv:Envelope>Info
For a user in a secondary user store, you should send the username in the format of
<user-store-domain>/<user-name>in above SOAP request. -
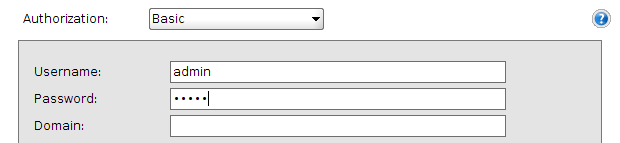
Add new a new basic authorization from the SOAP-UI request window and enter valid credentials to authenticate with the identity server.
Info
To try the scenario for a tenant user, provide the credentials of a tenant administer in the authentication step.
Info
In order to force a user to change the password after some specific time period, please refer " Configuring Password Policy Authenticator " documentation.
Related Links
See Configuring Claims for more information on how to store the claim values in the user store.