Configure Cross-Protocol Logout¶
This page guides you through enabling cross-protocol logout across different protocols such as SAML and OpenID Connect in WSO2 Identity Server.
Register the service providers¶
You need to register the two sample applications as service providers in WSO2 Identity Server.
Pickup Dispatch (SAML)¶
Follow the steps given below to register a SAML application as a service provider in WSO2 IS.
-
Log in to the management console (
https://<IS_HOST>:<PORT>/carbon) using admin/admin credentials. -
Navigate to Main > Identity > Service Providers and click Add.
-
Enter
saml2-web-app-pickup-dispatchin the Service Provider Name text box, and click Register. -
In the Inbound Authentication Configuration section, click Configure under the SAML2 Web SSO Configuration section.
-
Now set the configuration as follows:
- Issuer:
saml2-web-app-pickup-dispatch.com - Assertion Consumer URL:
http://localhost.com:8080/saml2-web-app-pickup-dispatch.com/home.jsp
Click Yes, in the message that appears.
- Issuer:
-
Select the following checkboxes:
- Enable Response Signing
- Enable Single Logout
- Enable Attribute Profile
- Include Attributes in the Response Always
- Enable Signature Validation in Authentication Requests and Logout Requests
Tip
For more information on the advanced configurations, see Advanced SAML Configurations.
-
-
Click Register to save the changes.
Pickup Manager (OIDC)¶
Follow the steps given below to register an OIDC application as a service provider in WSO2 IS.
-
Access the management console (
https://<IS_HOST>:<PORT>/carbon). -
Navigate to Main>Identity>Service Providers and click Add.
-
Enter pickup-manager in the Service Provider Name text box, and click Register.
-
In the Inbound Authentication Configuration section, click Configure under the OAuth/OpenID Connect Configuration section.
-
Enter the following value as the Callback URL:
http://localhost.com:8080/pickup-manager/oauth2clientTip
The callback URL is the service provider URL to which the authorization codes are sent. Upon successful authentication, the browser should be redirected to this URL.
-
Click Add. Note the OAuth Client Key and Client Secret that is displayed. You will need these values later on when deploying the sample application.
Tip
For more information on the advanced configurations refer, Advanced OAuth/OpenID Connect Configurations.
-
Click Register to save the changes.
Set up the Pickup Manager sample¶
Let's configure the Pickup Manager (OIDC) application to connect with WSO2 IS.
-
Download the pickup-manager.war sample.
-
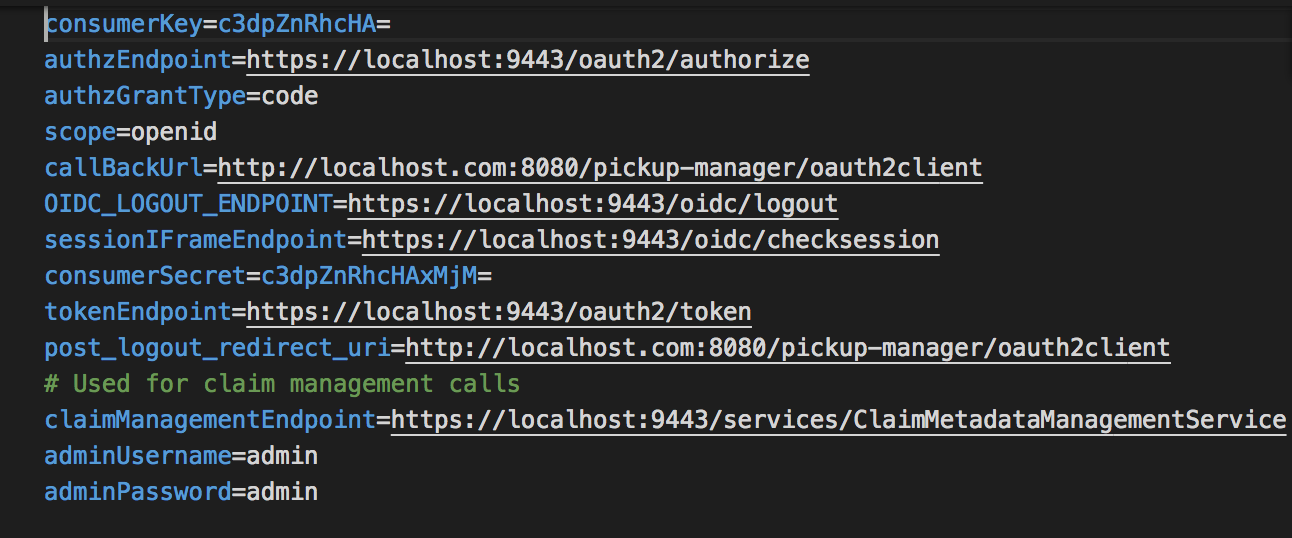
Extract the
pickup-manager.warfile and open themanager.propertiesfile located in the<EXTRACT>/WEB-INF/classesfolder. -
Replace the
consumerKeyandconsumerSecretvalues with the OAuth Client Key and Client Secret values that were generated for the newly created service provider.
Deploy the samples¶
Next, deploy the sample web apps on a web container.
-
Download Apache Tomcat 8.x from here and install. Tomcat server installation location will be referred as
<TOMCAT_HOME>later in this guide.Info
It is recommended that you use a hostname that is not
localhostto avoid browser errors. Modify the/etc/hostsentry in your machine to reflect this. Note thatwso2is.localis used in this documentation as an example, but you must modify this when configuring the authenticators or connectors with this sample application. -
To deploy the two applications:
-
Copy the extracted and modified OIDC
pickup-managerapplication folder to the<TOMCAT_HOME>/webappsfolder. -
Download the saml2-web-app-pickup-dispatch.com.war sample and copy it to the
<TOMCAT_HOME>/apache-tomcat-<version>/webappsfolder.
-
Try it¶
Once you have configured all your applications, access them in separate tabs in your browser. When you logout from one application, it should log you out from all the configured applications.
-
Access
http://wso2is.local:8080/saml2-web-app-pickup-dispatch.comon your browser and click Login. -
You will be redirected to the login page of WSO2 IS. Log in using your WSO2 IS credentials (
admin/admin). Provide the required consent. You will be redirected to the Pickup Dispatch application home page. -
Now, if you access
http://wso2is.local:8080/pickup-managerand click Login, you can see that user has been automatically logged in to this application without being prompted for user credentials. -
Click Admin on the top-right corner and click Logout to log out of the OIDC Pickup Manager application.
-
Switch to the SAML Pickup Dispatch app on your browser. You will see that you have been logged out of the SAML application as well.
You have successfully tried out cross-protocol logout between a SAML application and an OIDC application.
Related topics