Add GitHub login¶
You can add GitHub login to your applications using WSO2 Identity Server and enable users to log in with their GitHub accounts.
Follow this guide for instructions.
Register WSO2 Identity Server on GitHub¶
You need to register WSO2 Identity Server as an OAuth app on GitHub.
Note
You can follow the GitHub documentation for detailed instructions.
- Log in to GitHub, click your profile icon, and click Settings.
- On the left panel of the Settings page, click Developer settings.
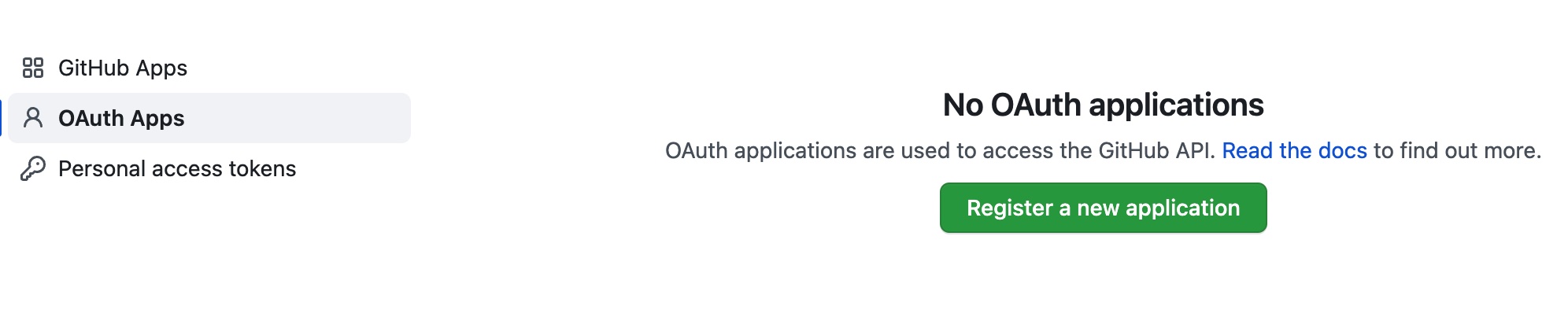
-
Under OAuth apps, click Register a new application.
-
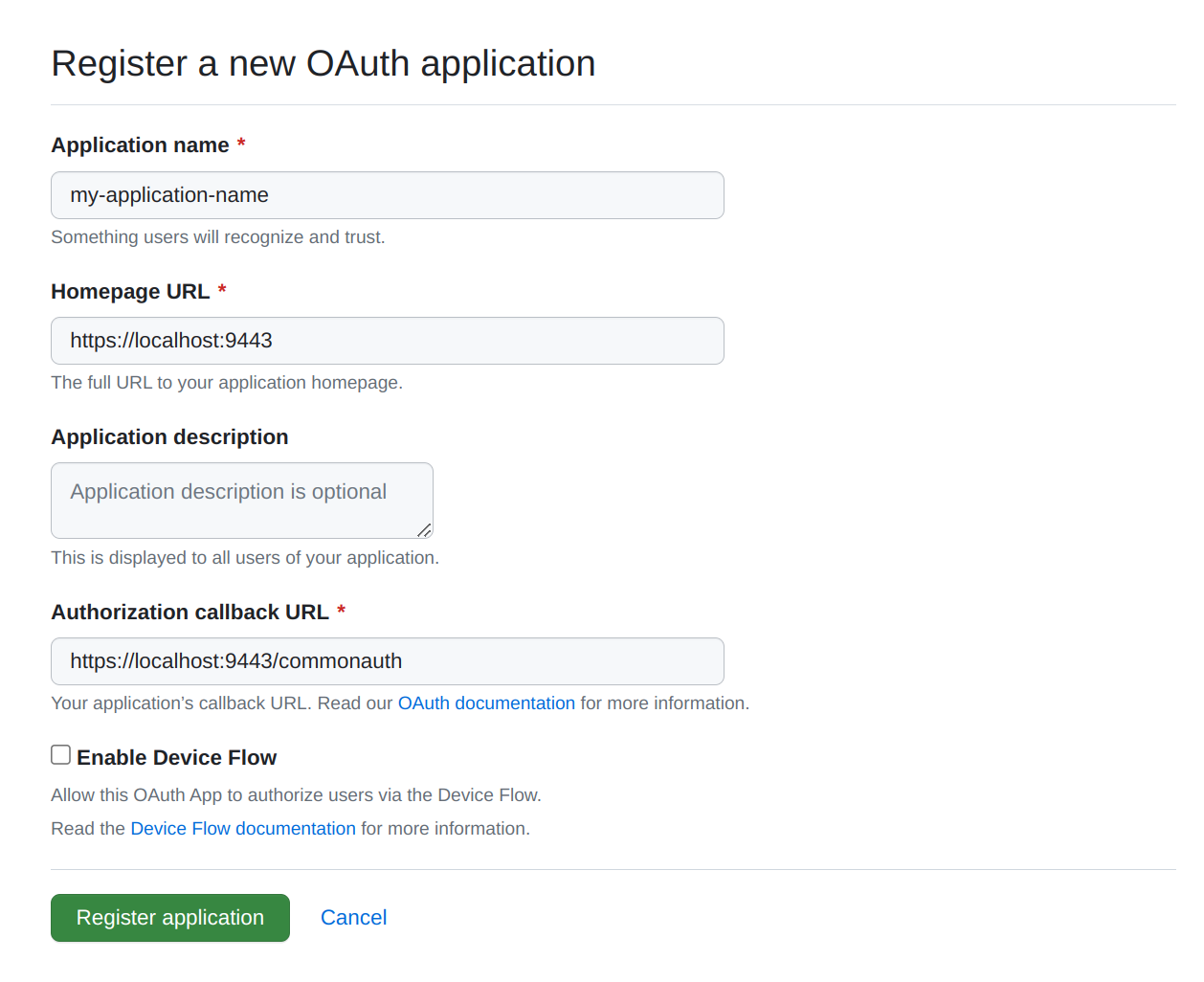
Give the application a name and the following URLs:
-
Homepage URL
-
Authorization callback URL
-
-
Click Register application.
- Generate a new client secret and take note of the Client ID and Client secret.
Register the GitHub IdP¶
Now, let's register the GitHub IdP in WSO2 Identity Server.
- On the WSO2 Identity Server Console, go to Connections.
- Click New Connections and select GitHub.
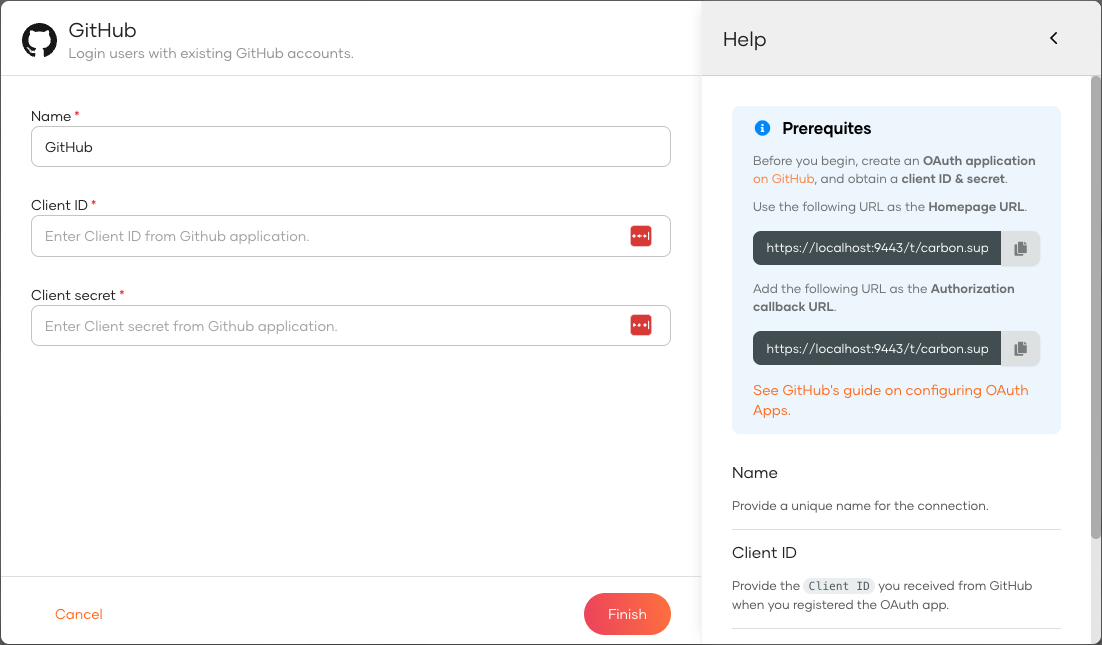
-
Enter the following details and click Finish:
Parameter Description Name A unique name for this GitHub identity provider. Client ID The client ID obtained from GitHub. Client secret The client secret obtained from GitHub. -
Go to the Settings tab and see the list of scopes to which GitHub has granted permissions.
- email: Grants read access to a user's primary email address.
- public_profile: Grants read access to a user's default public profile details.
Note
WSO2 Identity Server needs these scopes to get user information. WSO2 Identity Server checks the attribute configurations of the application and sends the relevant attributes received from GitHub to the app. You can read the GitHub Documentation to learn more.
Enable GitHub login¶
Before you begin
You need to register an application with WSO2 Identity Server. You can register your own application or use one of the sample applications provided.
- On the WSO2 Identity Server Console, go to Applications.
-
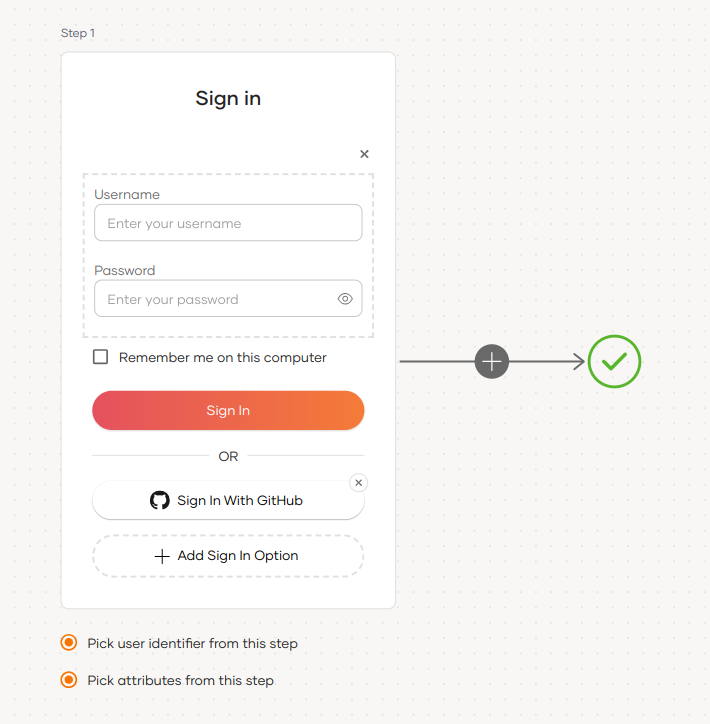
Select your application, go to the Login Flow tab and add GitHub login from your preferred editor:
-
Click Add Sign In Option to add a new authenticator to the first step.
-
Select the GitHub connection.
-
Click Confirm to add login with GitHub to the sign-in flow.
Recommendations
It is recommended to add your social and enterprise connections to the first authentication step as they are used for identifying the user.
-
-
Click Update to save your changes.
Try it out¶
Follow the steps given below.
-
Access the application URL.
-
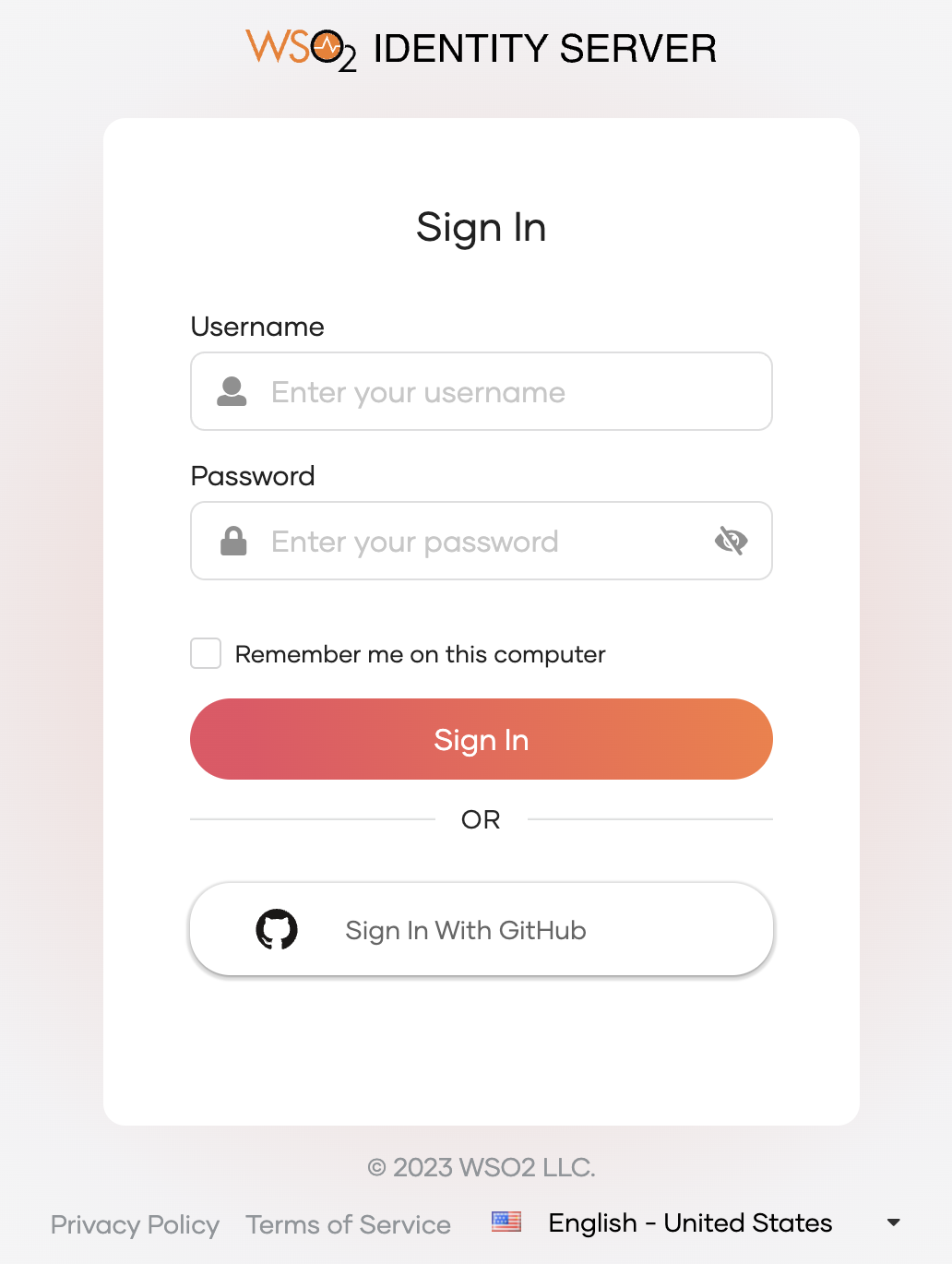
Click Login to open the WSO2 Identity Server login page.
-
On the WSO2 Identity Server login page, Sign in with GitHub.
-
Log in to GitHub with an existing user account.
Note
When a user successfully logs in with GitHub for the first time, a user account is created in the WSO2 Identity Server Console with the GitHub username. This new user account will be managed by GitHub.
Configure connection¶
To learn more about other configurations available for the connection, refer to the add federated login documentation.