Outbound Provisioning with Google¶
The WSO2 Identity Server (WSO2 IS) has the ability to provision users into different domains like Salesforce, Google, Facebook, etc., using its identity provisioning framework .
This topic provides instructions on how to configure Google as the Identity Provider to provision users from WSO2 Identity Server. The service provider in this scenario is WSO2 Identity Server(WSO2 IS). When WSO2 Identity Server is the service provider, it is configured as the resident Service Provider. Therefore, after completing this tutorial you can see the users you add using WSO2 Identity Server being created in Google too.
Before you begin!
- You need to have a Google domain. Click here for more information on creating the domain.
Configuring Google¶
In this section, you are going to create a service account using the Google domain you created before you started this guide.
-
Open the Google developers console to create a new project.
-
Create a new project:
-
Click CREATE PROJECT on the top of the page.
-
Provide a name for your project and click Create.
-
-
Search for the project you created and click it.
-
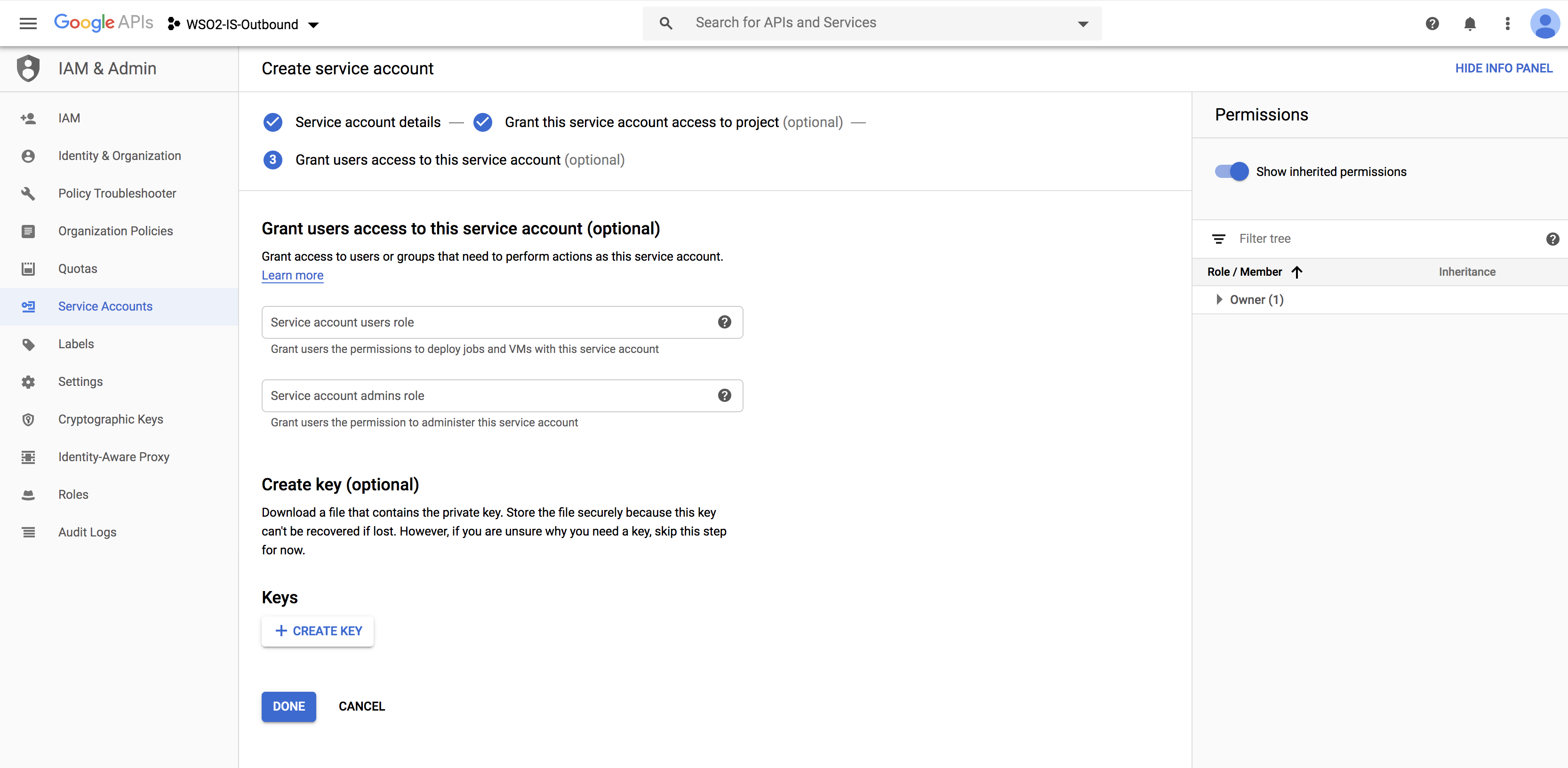
Create a service account for the project you created.
-
Click IAM and admin > Service accounts.
-
Fill in the form to create the service account:
-
Click CREATE.
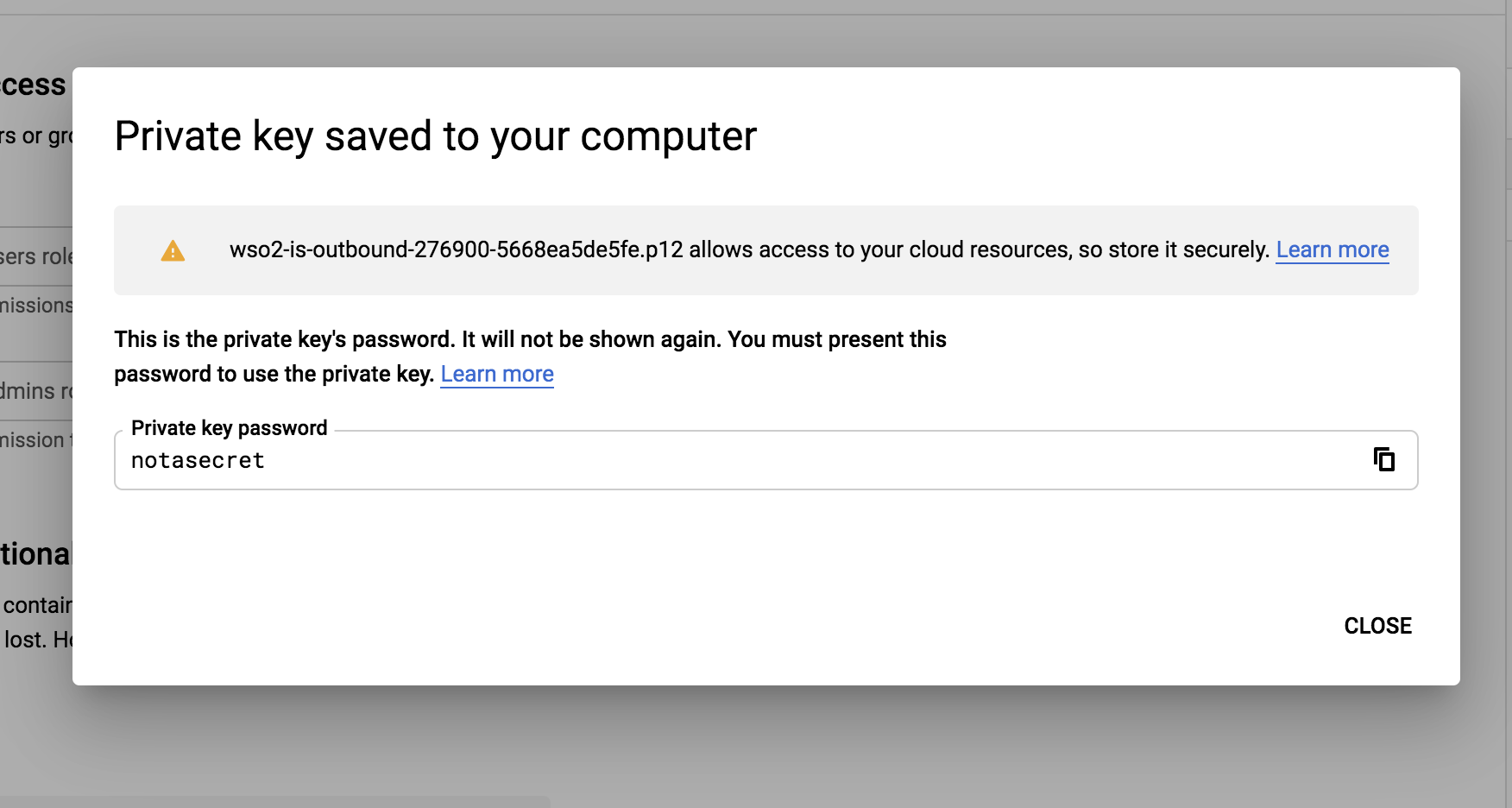
The Service account and key created message is displayed and the service account'sP12file is downloaded to your machine.Info
Remember the location and name of this downloaded file as it is required later on in this guide.
-
-
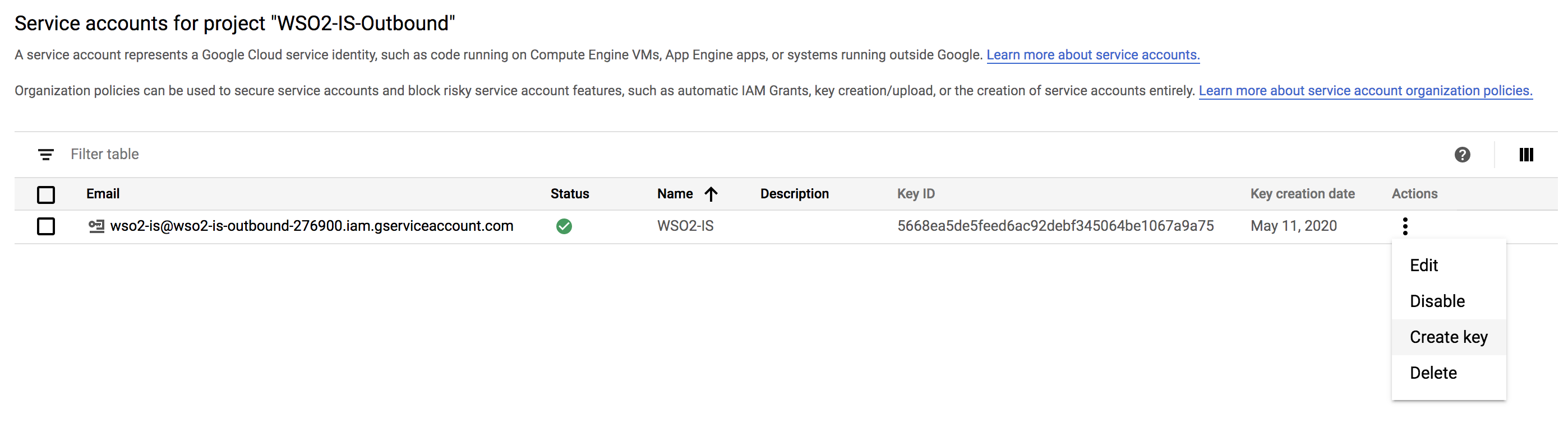
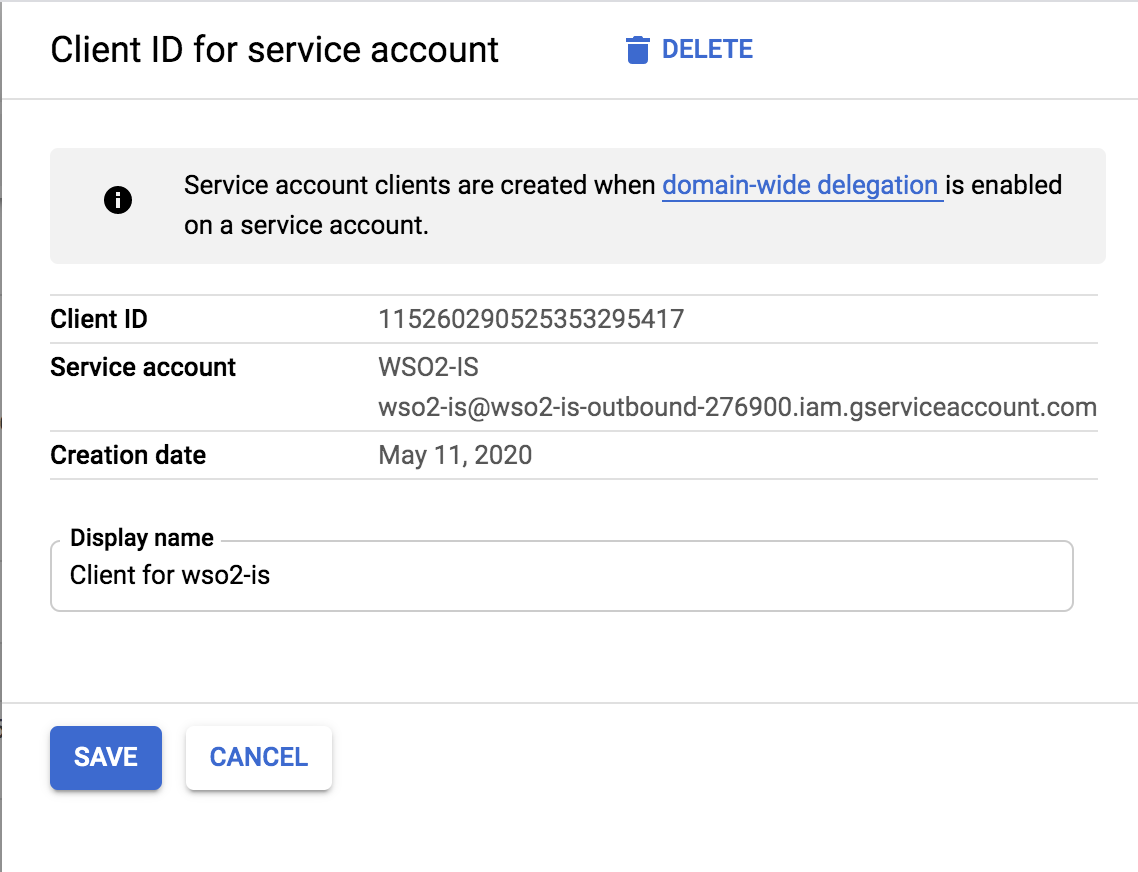
Get the Client ID of the service account.
-
Manage the API client access:
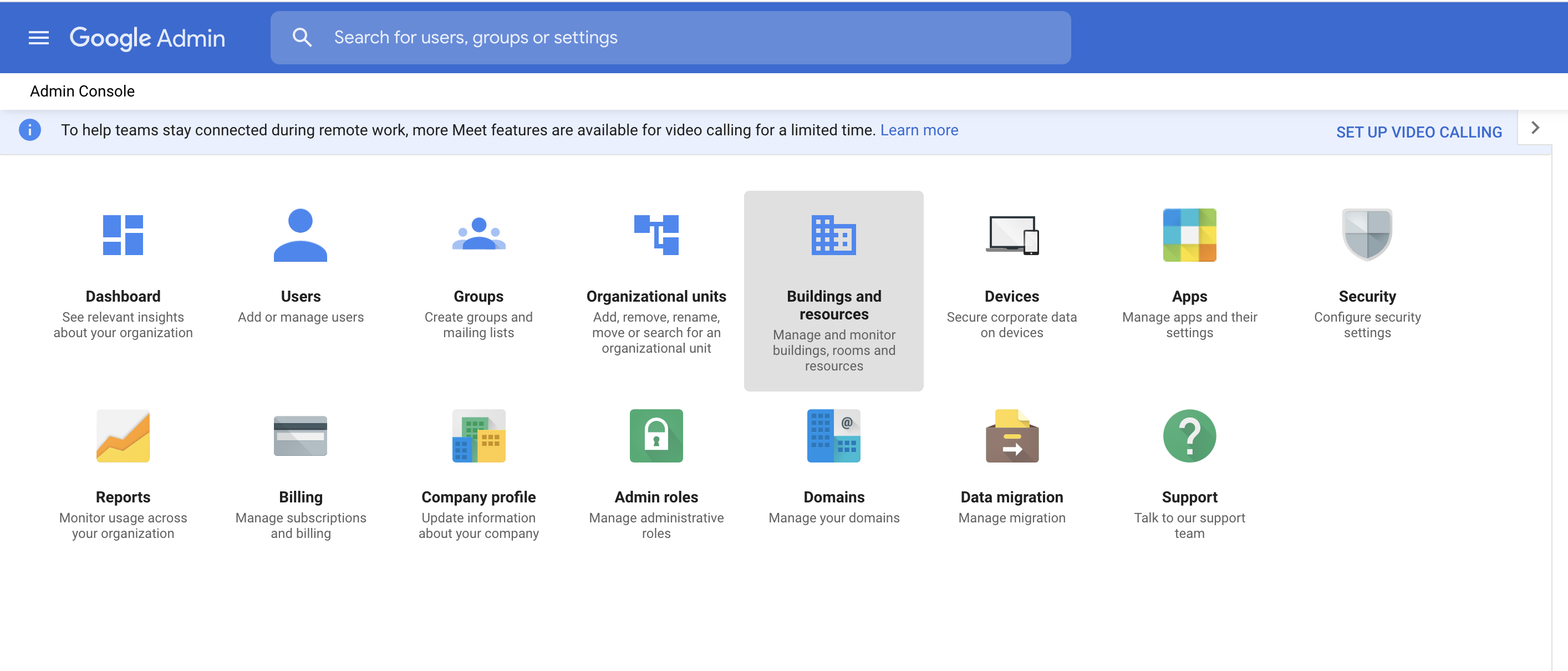
- Go to your domain's admin console via https://admin.google.com.
-
Click Security.
-
Click Advanced settings > Manage API client access.
-
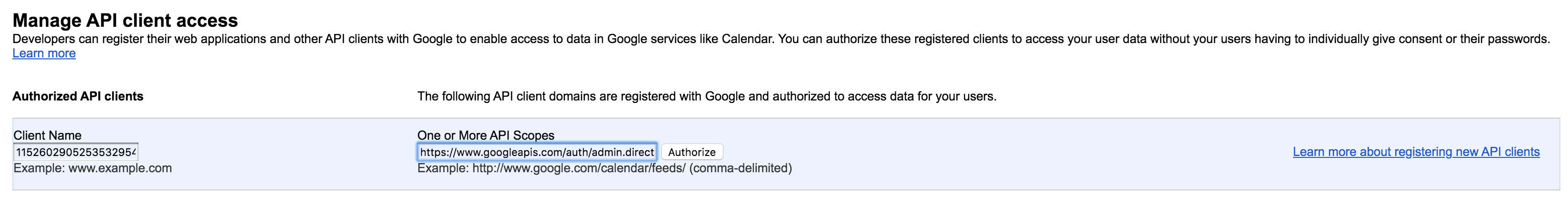
Fill the following values:
- Paste the Client ID value you copied previously as the value for Client Name.
- Enter
https://www.googleapis.com/auth/admin.directory.user,https://www.googleapis.com/auth/admin.directory.orgunit,https://www.googleapis.com/auth/admin.directory.groupas the value for scopes. - Click Authorize.
-
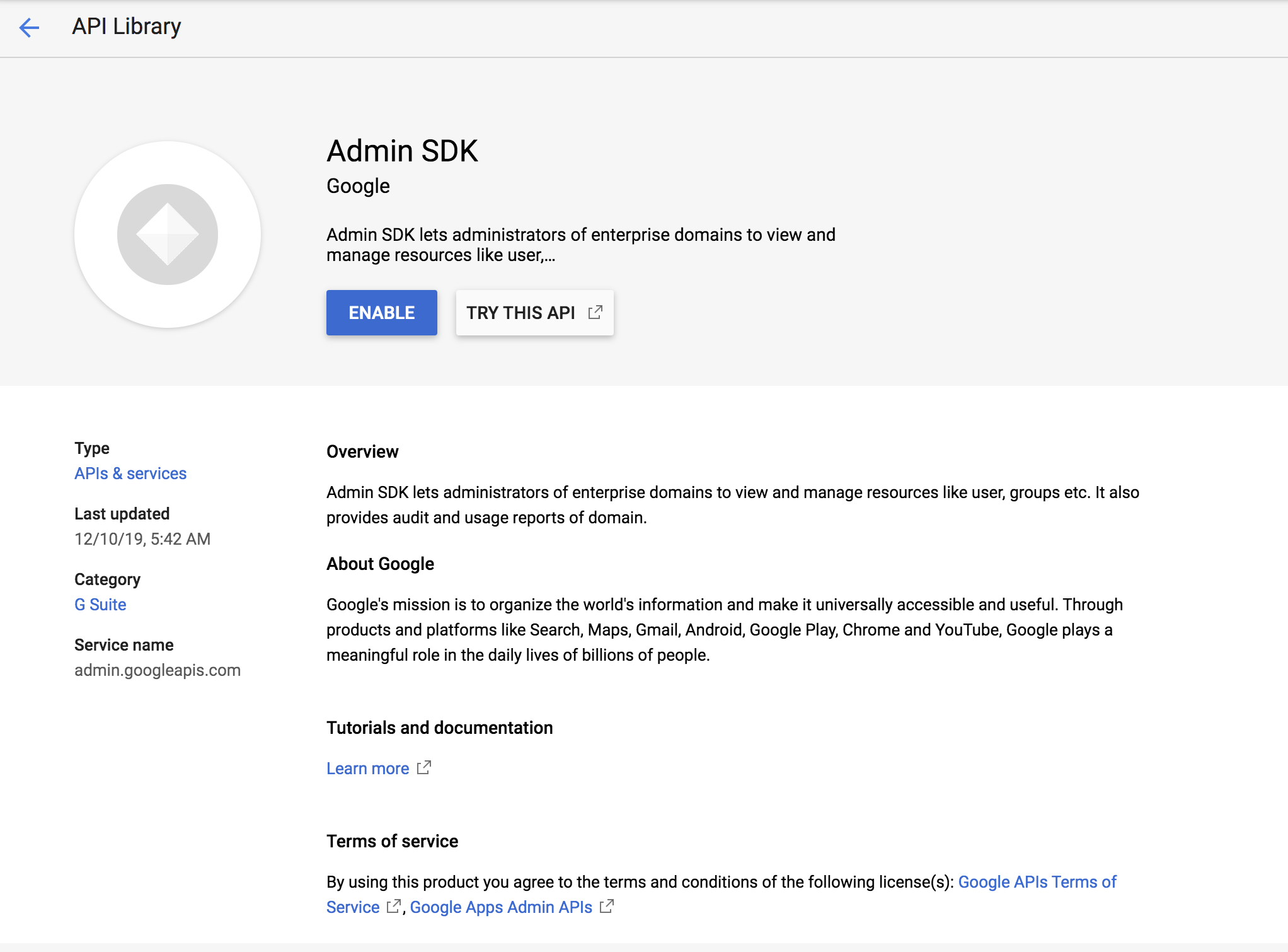
Enable Admin SDK.
- Open the Google developers console.
- Click the menu icon, and click APIs & Services > Dashboards.
- Click on Enable APIs AND Services.
-
Search for Admin SDK and click Enable.
Configuring the Identity Server to use email address as the username¶
Provisioning is the process of coordinating the creation of user accounts, e-mail authorizations in the form of rules and roles, and other tasks such as provisioning of resources associated with enabling new users.
- Download the WSO2 Identity Server from here.
- When you log into Google, you normally use an email address. So, to integrate this with the Identity Server, you need to configure WSO2 IS to enable users to log in using their email addresses. In order to do that, follow the steps found in the Using Email Address as the Username topic.
-
Restart the Identity Server. Since the username and password of the admin user were updated, start the WSO2 IS server using the -Dsetup parameter as shown in the command below.
sh wso2server.sh -Dsetup
Now that you are done with configuring WSO2 Identity Server to use the email address, configure the identity provider and the service provider.
Configuring Google as the Identity Provider¶
This section includes steps on how to register Google as an Identity Provider.
- Start the WSO2 Identity Server if it is not started up already, and log in using the email you configured for the realm configurations as instructed above in step 2 of Configuring the Identity Server to use the email address as the username.
- On the Management Console, click on Add under Identity Providers.
-
In the form that appears, provide a name for your identity provider by filling in the Identity Provider Name, such as Google.com, and a description.
Info
See Configuring an Identity Provider for more information on registering and configuring an identity provider.
-
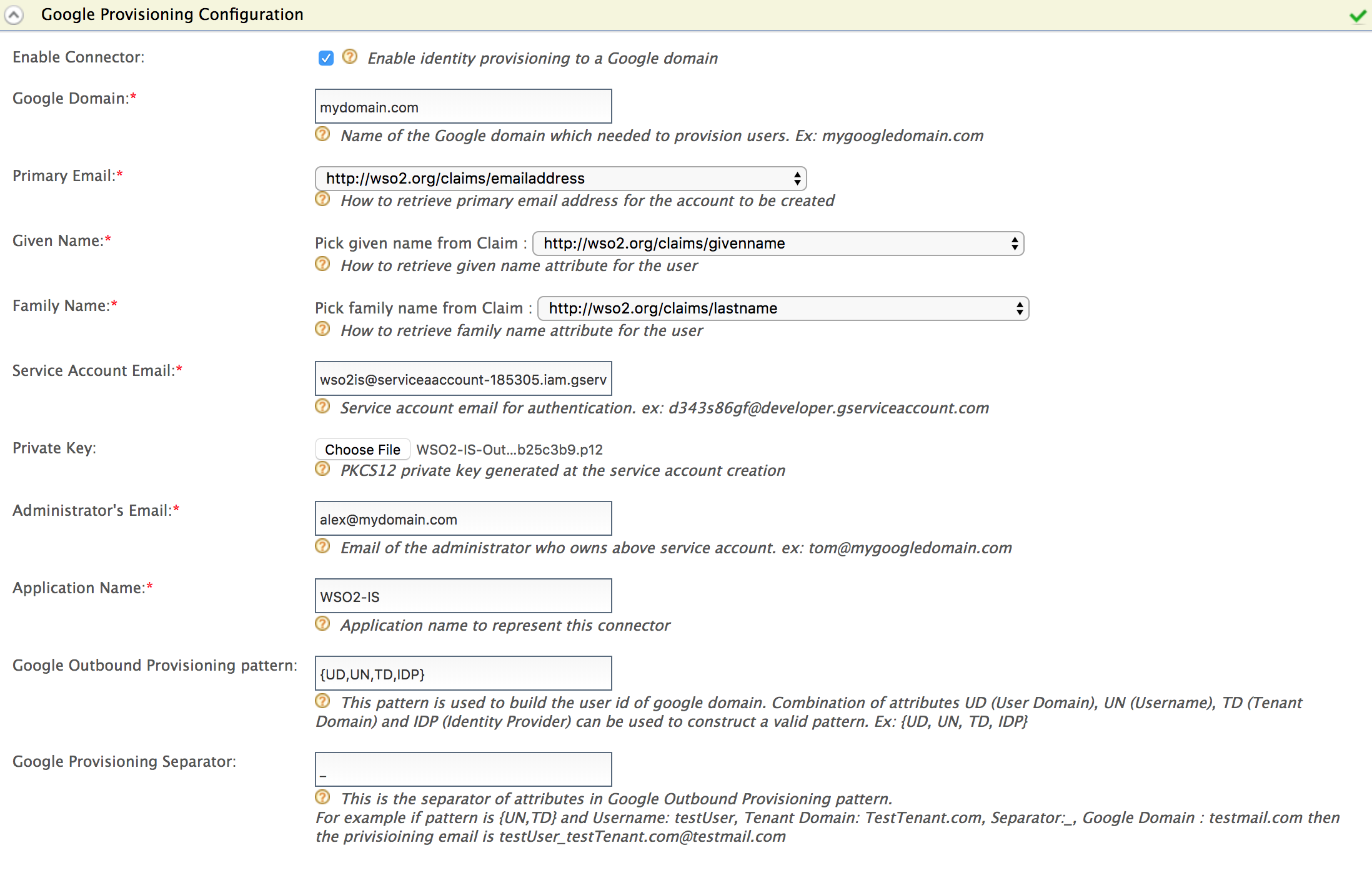
Expand the Outbound Provisioning Connectors and click Google Provisioning Configuration section.
-
Do the following configurations for Google provisioning.
Info
For more information on any of these fields, see Configuring Google provisioning
.
- Select Enable Connector to enable the Google connector.
- Enter your Google domain name.
For example, in this guide, mydomain.com is used as the domain name. - Select the claim URI for the Primary Email.
For example, use http://wso2.org/claims/emailaddress. - Select the claim URI for the Given name.
For example, use http://wso2.org/claims/givenname. - Select the claim URI for the family name.
For example, usehttp://wso2.org/claims/lastname. -
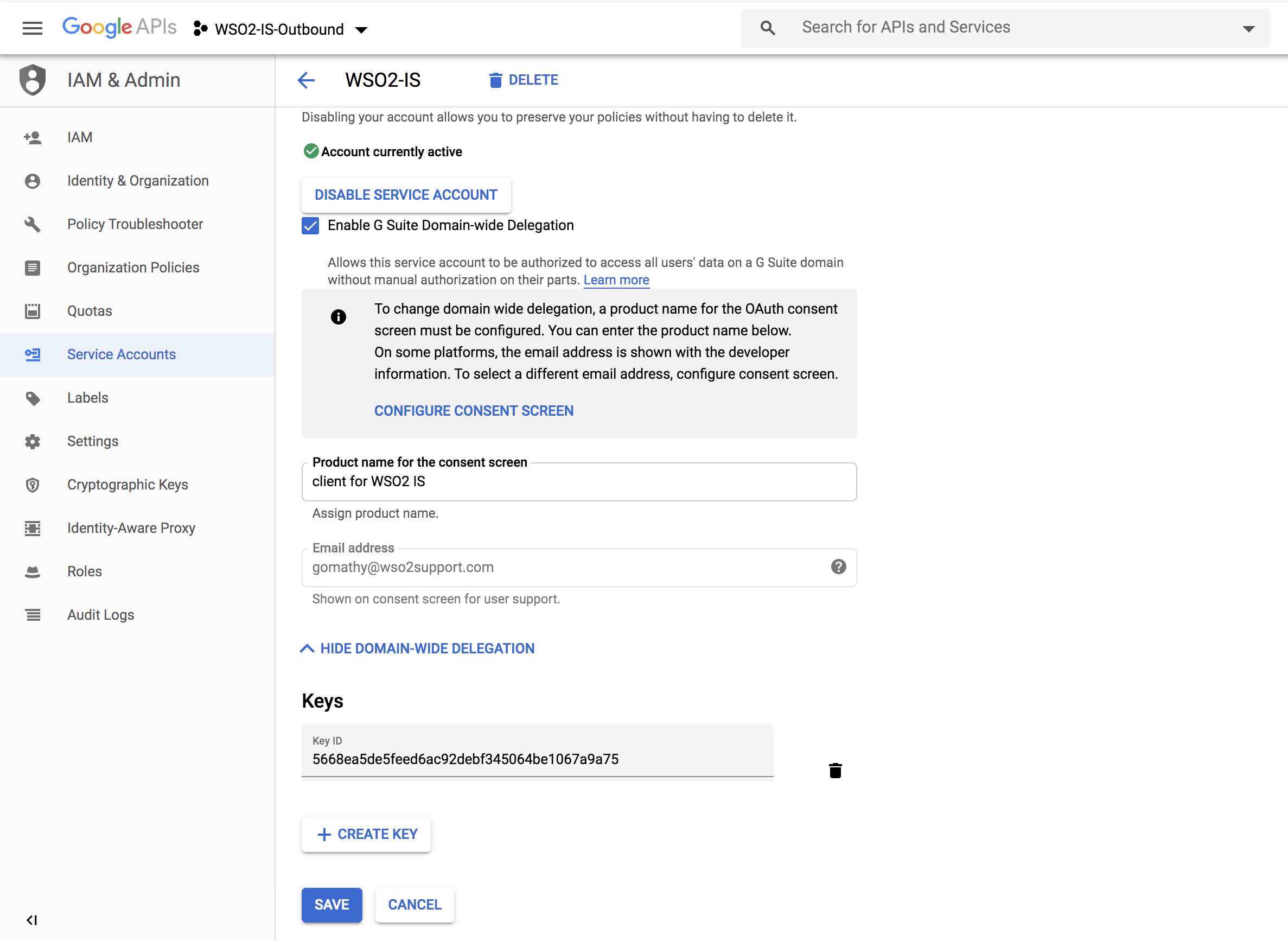
Enter your service account ID as the value for the Service Account Email.
Can't remember your service account ID?
Follow the steps given below:
- Open the Google developers console and click the Menu icon in the top left corner.
- Click IAM and admin > Service accounts.
- Note the service account ID of your service account.
-
Attach the private key you downloaded in step 4.e under Configuring Google as the Private Key.
- Enter the email address you created using your domain before starting this tutorial as the Administrator's Email.
- Enter a name for your application in the Application Name field. It is used to help you identify requests made by this Google client.
- Enter {UD,UN,TD,IDP} as the value for Google Outbound Provisioning Pattern. This pattern is used to build the user id of Google domain.
- Enter _ (the underscore character) as the value for the Google Provisioning Separator.
-
Click Register.
Configuring WSO2 IS as the resident Service Provider¶
With outbound provisioning, the users you create in one application or service provider needs to be stored in the Google identity provider you just created. For this scenario, WSO2 Identity Server acts as the service provider, so we need to add it as a resident service provider. For more information on the resident service provider, see Configuring a resident service provider .
- In the Main menu under the Identity section, click Resident under Service Providers.
- Expand the Outbound Provisioning Configuration on the screen that appears.
-
Select the Google identity provider you configured from the drop down and click the
 button.
button.Info
If you enable Blocking, Identity Server will wait for the response from the Identity Provider to continue.
If you enable Enable Rules and Blocking, blocking will block the provisioning till the rule completely evaluates and get the response back to the WSO2 IdP. Afterwards, you need to enable the XACML policy. For more information, see Rule-Based Provisioning
-
Click Update.
Working with users¶
The next step is to check if Google is configured properly with the Identity Server. If you add a user to the Identity Server via the management console, this user should also appear in Google too.
- On the Main tab in the Management Console, click Add under Users and Roles.
- Click Add New User.
-
Enter the username in the form of an email and enter the password.
Info
Later on, if you want to update the user details, you won't be able to update the email address.
-
Assign a role to the user.
- Click Finish.
- In Google, log into admin console of your domain.
On the left navigation pane, expand Users and click Users. You will see that the user you created in the Identity Server has been added to Google as well.
You have successfully completed the configurations to provision users from WSO2 IS to Google.
What's next?¶
- If you want to JIT provision users from Google to WSO2 Identity Server in this use case, see Configuring Just-In-Time Provisioning for an Identity Provider .
- You can configure WSO2 IS to outbound provision users only if a given XACML rule is met. For more information, see Rule-Based Provisioning.